Introduction
The JS7 - Profiles hold settings that are specific for a user and that are controlled by the user.
- Profiles include a number of categories such as Preferences, Permissions etc.
- The profile includes settings used for digitally signing objects such as workflows for JS7 - Deployment.
- The underlying security requirements are explained with JS7 - Secure Deployment.
The JS7 - Security Architecture suggests to operate JOC Cockpit in one of the following security levels:
- Security Level Low
- Inventory objects are automatically signed with the private key that is stored with the
rootaccount. - Signing is automatically applied when performing the Deploy operation.
- The Profile page for Signature Key Management is available for the user account only that is specified as the default profile account with the JS7 - Settings, chapter: JOC Cockpit Settings.
- Inventory objects are automatically signed with the private key that is stored with the
- Security Level Medium
- Inventory objects are automatically signed with the private key that is stored with the current user's account.
- Signing is automatically applied when performing the Deploy operation.
- The Profile page for Signature Key Management is available individually for any user accounts holding a Deploy permission, see JS7 - Default Roles and Permissions.
- Security Level High
- Inventory objects are signed outside of JOC Cockpit.
- As a consequence no Profile page for Signature Key Management is available.
The article is intended for a security-aware audience that is technically familiar with digital key management. JS7 supports both X.509 and PGP certificates, the following explanations are focused on use of X.509 certificates.
Profile Page
The Profile page is accessible from the user menu of an account in the right upper corner of any JOC Cockpit view:
The Profile page offers a number of sub-views. The following section explains the Signature Key Management sub-view.
Signature Key Management
The Signature Key Management sub-view offers the following settings:
CA Certificate
Users have the option to
- use a CA-signed certificate
- created by the JS7 - Certificate Authority available with JOC Cockpit,
- created by their own or by a trusted 3rd-party Certificate Authority,
- use a self-signed certificate.
Use of CA certificates includes that
- the CA Certificate is required to verify the user account's private key and certificate for digital signing when performing deployments.
- This includes to check that the user account's certificate is signed with the given CA Certificate or a later CA Intermediate Certificate.
- This includes to check expiration dates of certificates.
- Depending on the fact if the JS7 Certificate Authority or if an external Certificate Authority is used the respective CA Certificate has to be added to the user account's Profile.
- for an X.509 CA Certificate (Root CA Certificate or Intermediate CA Certificate) the certificate's subject is displayed.
Operations for CA Certificates include to
- view the CA Certificate by use of the icon,
- update the CA Certificate by use of the icon,
- import the CA Certificate by use of the icon.
View CA Certificate
A CA Certificate is displayed like this:
Update CA Certificate
A CA Certificate can be updated by pasting from the clipboard like this:
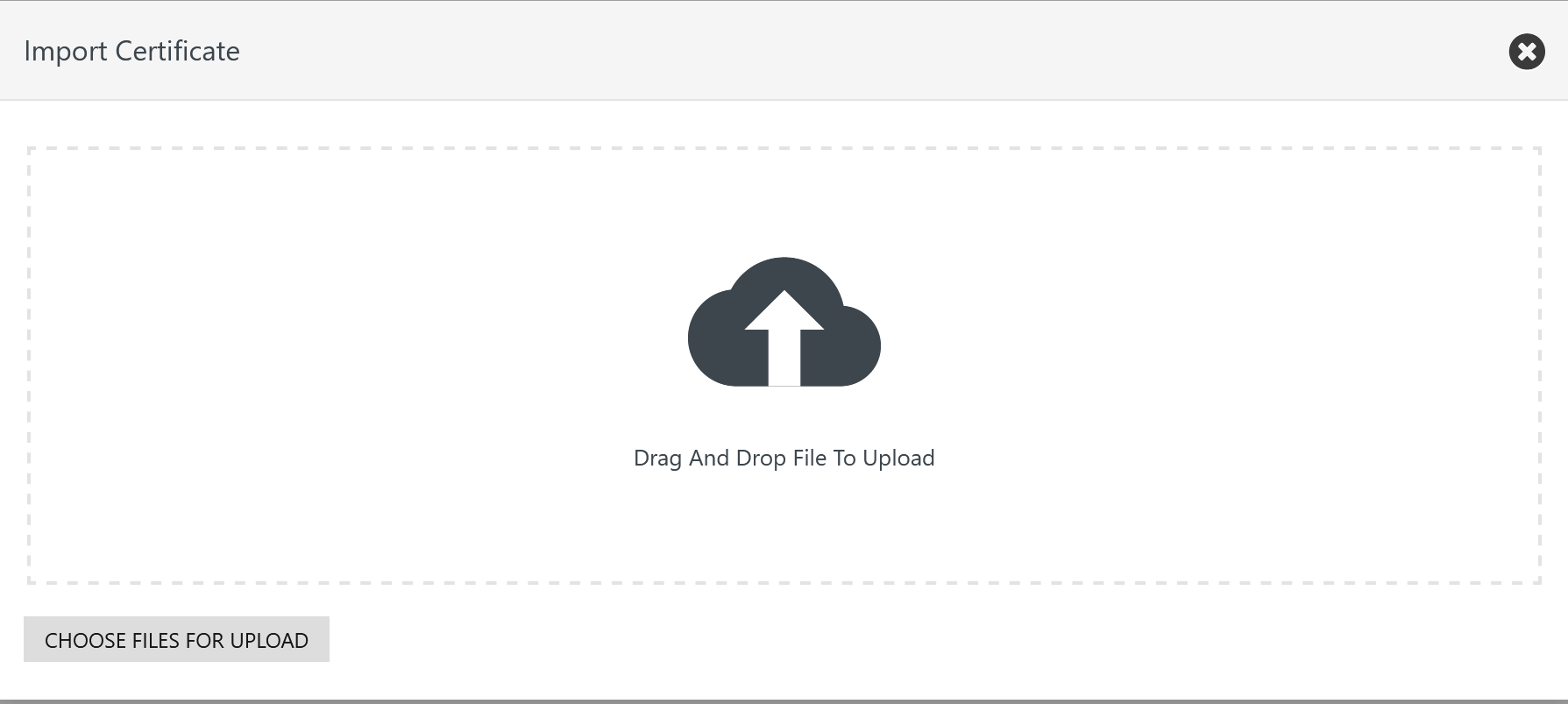
Import CA Certificate
A CA Certificate can be imported from a file like this:
Keys and Certificates
User accounts have to be equipped with a private key and certificate issued for digital signing in order to deploy scheduling objects to Controllers and Agents:
- If the user's certificate is signed by a Certificate Authority then it is sufficient to rollout the CA Certificate to Controller and Agent instances to which the user should be entitled to deploy scheduling object such as workflows.
- if the user's certificate is self-signed then the user's certificate has to be rolled out to Controller and Agent instances to which the user should be entitled to perform deployments.
Users have options about the issuer of private keys and certificates:
- Use of the built-in JS7 Certificate Authority
- JOC Cockpit offers to sign a user account's public key for digital signing from its built-in CA, see JS7 - Certificate Authority
- In a single operation users can generate a private/public key pair and make the JS7 Certificate Authority sign their public key to a certificate.
- Use of an external Certificate Authority
- If an external CA should be consulted then users have to create a Certificate Signing Request (CSR) outside of JOC Cockpit and make their external CA sign this request. The resulting certificate can be added to the user's Profile in JOC Cockpit.
- If users do not operate a CA or do not dispose of certificates then they can continue to use the default private key and certificate that ship with JOC Cockpit.
- In this situation by default the
rootaccount only can be used to deploy scheduling objects such as workflows which suggests to operate JOC Cockpit for Security Level Low as therootaccount's key and certificate will be used for signing deployments by any users accounts. - For a Security Level Medium each user account has to be equipped with a private key and certificate.
- In this situation by default the
Operations for the user account's private key and certificate include to
- view the private key and certificate by use of the icon,
- update the private key and certificate by use of the icon,
- import the private key by use of the icon,
- generate the private key by use of the icon.
View Key and Certificate
The user account's private key and certificate for digital signing is displayed like this:
Update Key and Certificate
A user account's private key and certificate can be created by an external CA and can be updated by pasting from the clipboard like this:
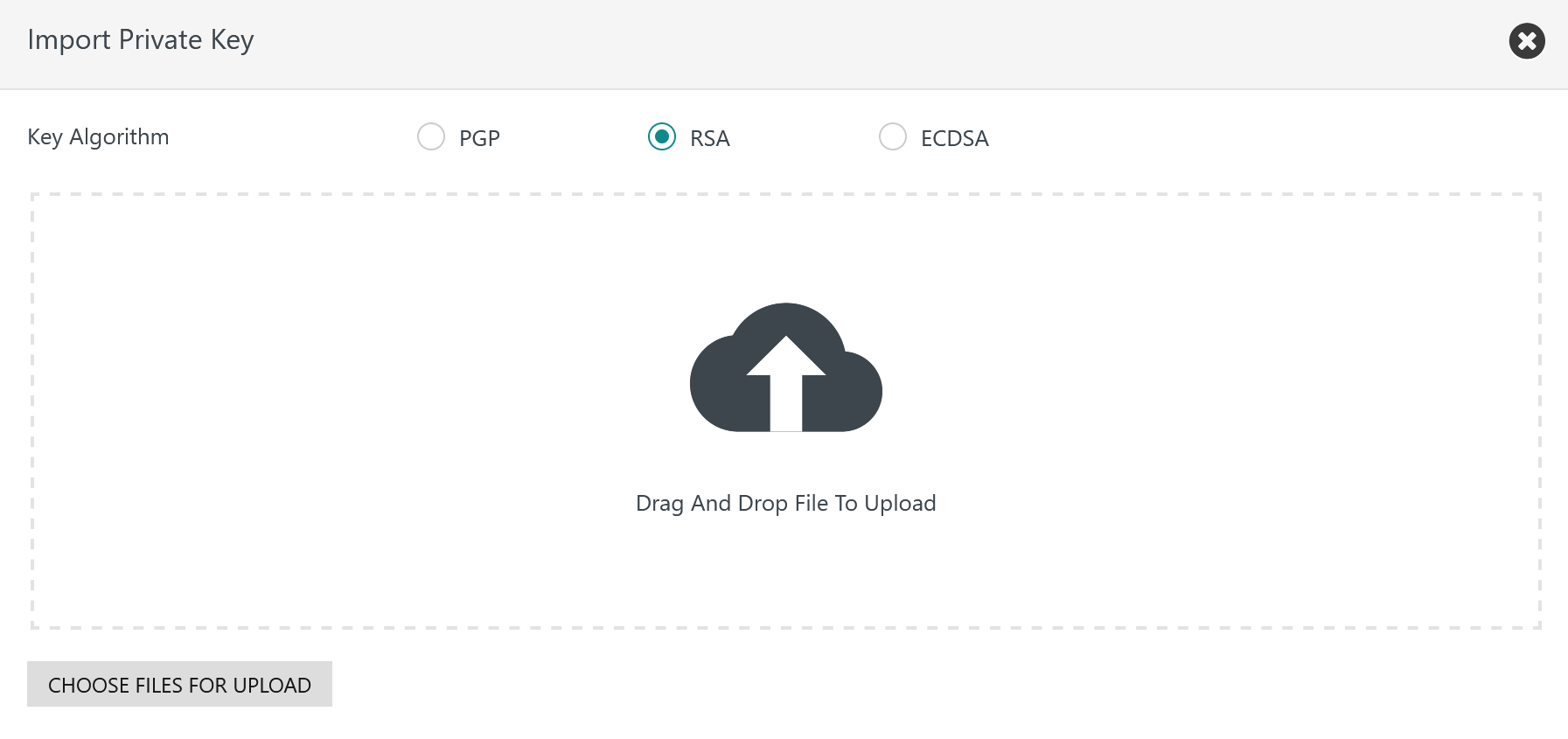
Import Key
A user account's private key can be created by an external CA and can imported from a file like this:
Consider that an X.509 certificate matching the user account's private key has to be signed by a CA and has to be added by use of the Update Key and Certificate operation as explained above.
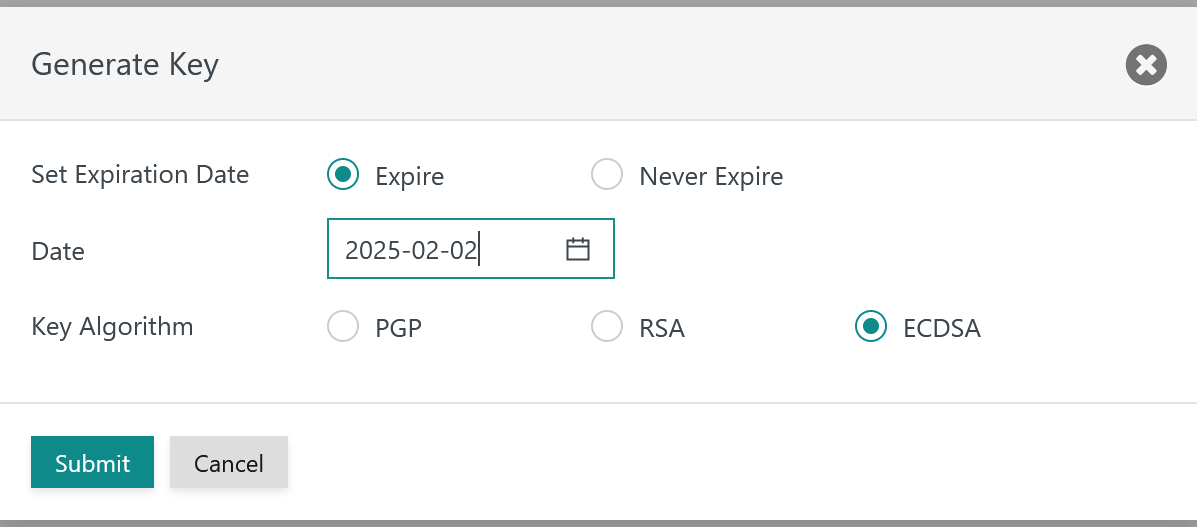
Generate Key
A user account's private key and optionally the certificate can be generated like this:
Use of Key Algorithms
- When choosing Key Algorithm
PGPorRSAthen a private key only is createdConsider that an X.509 certificate matching the user account's public key is signed by an external CA and has to be added by use of the Update Key and Certificate operation as explained above.
- When choosing Key Algorithm
ECDSAthen a private key is created and a CA-signed certificate is created if the JS7 Certificate Authority is in use.