Introduction
- Identity Services implement authentication methods and access to Identity Providers, for example credentials such as account/password are used as an authentication method to access an LDAP Directory Service as the Identity Provider, see JS7 - Identity and Access Management.
- JOC Cockpit implements a pluggable architecture that allows to add Identity Service products with future JS7 releases.
- For compatibility reasons early releases of JS7 include the Shiro Identity Service, see
JOC-1145
-
Getting issue details...
STATUS
- FEATURE AVAILABILITY ENDING WITH RELEASE 2.3.0
Matrix of Identity Services
Identity Services can be used in a number of flavors depending on the fact
- which application manages user accounts/passwords:
- a specific application of the Identity Service,
- JOC Cockpit that propagates user accounts/passwords to the Identity Service but does not store such credentials with its database.
- where assignments of roles to user accounts are stored
- with the Identity Service
- with the JS7 database
| Identity Service | Identity Service Configuration Items | JOC Cockpit Configuration | ||||
|---|---|---|---|---|---|---|
| Service ID | Built-in | User Accounts/Passwords stored with | User Accounts/Passwords managed by | Roles/Permissions stored with | Assignment Roles->User Accounts stored with | Roles Mapping |
| JOC | yes | Database | JOC | Database | Database | n/a |
| LDAP-JOC | yes | LDAP Server | LDAP | Database | Database | n/a |
| LDAP | yes | LDAP Server | LDAP | Database | LDAP Server | Mapping of LDAP Security Groups to JOC Cockpit Roles |
| Vault-JOC | no | Vault Server | Vault | Database | Database | n/a |
| Vault-JOC-ACTIVE | no | Vault Server | Vault, JOC | Database | Database | n/a |
| Vault | no | Vault Server | Vault | Database | Vault Server | Mapping of Vault Policies to JOC Cockpit Roles |
| Keycloak-JOC | no | Keycloak Server | Vault | Database | Database | n/a |
| Keycloak-JOC-ACTIVE | no | Keycloak Server | Keycloak, JOC | Database | Database | n/a |
| Keycloak | no | Keycloak Server | Keycloak | Database | Keycloak Server | Mapping of Keycloak Policies to JOC Cockpit Roles |
| Shiro (deprecated) | yes | shiro.ini | shiro.ini | shiro.ini | shiro.ini | n/a |
Manage Identity Services
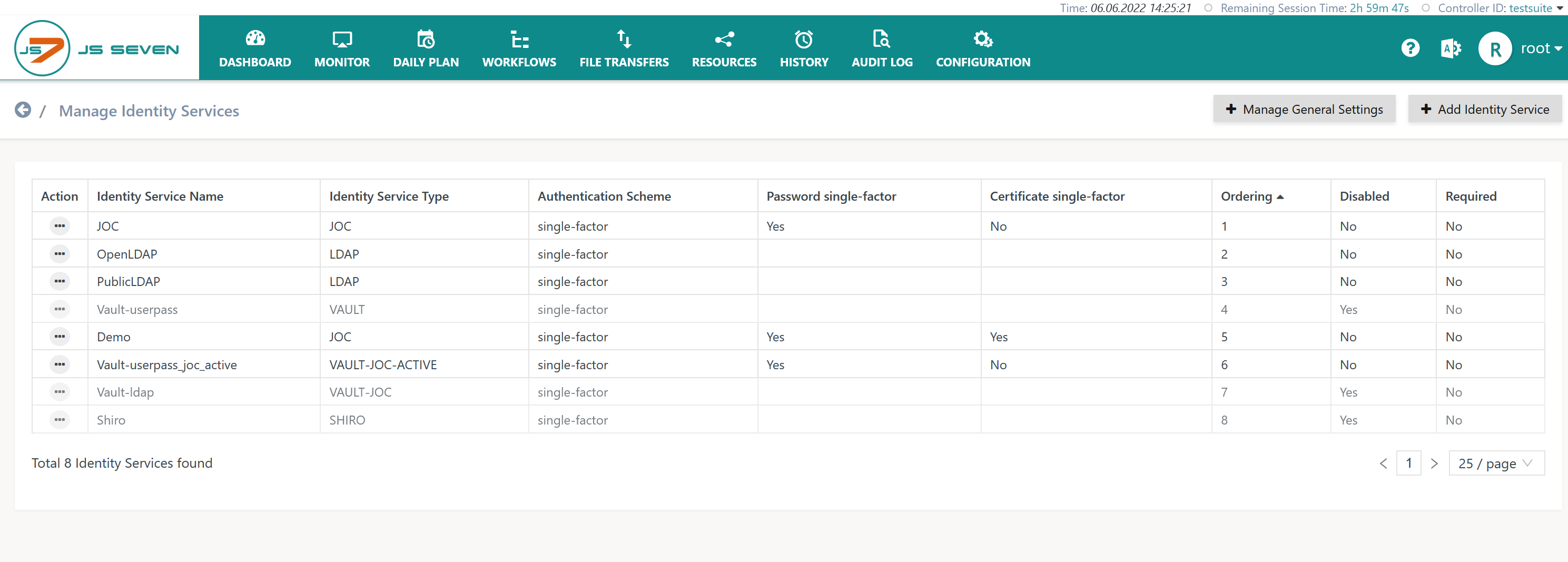
The operation to manage Identity Services is available from the user menu in the right upper corner of any JOC Cockpit page:
This operation brings forward the list of available Identity Services.
- By default the built-in JOC Identity Service is available.
- The Shiro Identity Service is available for migration purposes up to release 2.3.0.
Add Identity Service
To add an Identity Service use the respective button from the list of Identity Services:
Explanation:
- The
Nameof the Identity Service can be freely chosen. - The Identity Service
Typecan be selected as available from the above matrix. - The
Orderingspecifies the sequence in which a login is performed with available Identity Services. - The
Requiredattribute specifies if a login with the respective Identity Service is required to be successful.
Manage Settings
Settings are available at a global level and per Identity Service.
Global Settings
Global settings are applied for all Identity Services.
- At the time of writing a single setting for the max. idle timeout of user sessions is applied.
- Should the lifetime of a token provided by an external Identity Service be different from the max. idle timeout then JOC Cockpit will try to renew the token with the Identity Service. Renewal of a token does not require the user to repeatedly specify credentials for login.
- Identity Services can restrict the lifetime of tokens and they can deny renewal of tokens. If a token cannot be renewed then the user session is terminated and the user is required to perform a login.
Vault Identity Service Settings
For use of the HashiCorp® Vault Identity Service
- the Vault product has to be installed and accessible for JOC Cockpit,
- the following settings have to be specified:
Explanation:
Vault URL: the base URL for which the Vault REST API is availableVault Keystore Path: Should the Vault REST API be configured for HTTPS Mutual Authentication then the indicated keystore has to include the private key specified for the extended key usage ofClient Authentication.Vault Keystore Password: Should the Vault REST API be configured for HTTPS Mutual Authentication and the indicated keystore be protected by a password then the password has to be specified.Vault Key Password: Should the Vault REST API be configured for HTTPS Mutual Authentication and the indicated private key be protected by a password then the password has to be specified.Vault Keystore Type: Should the Vault REST API be configured for HTTPS Mutual Authentication then the type of the indicated keystore has to be specified being eitherPKCS12orJKS.Vault Truststore Path: Should the Vault REST API be configured for HTTPS then the indicated truststore has to include an X.509 certificate specified for the extended key usage ofServer Authentication. This can be a self-signed server certificate or a CA-signed certificate (typically the Root CA certificate is used as otherwise the complete certificate chain involved in signing the server certificate has to be available with the truststore).Vault Truststore Password: Should the Vault REST API be configured for HTTPS and the indicated truststore be protected by a password then the password has to be specified.Vault Truststore Type: Should the Vault REST API be configured for HTTPS then the type of the indicated truststore has to be specified being eitherPKCS12orJKS.Vault Application Token: The application token has to be created by Vault for JOC Cockpit. It allows to access the Vault REST API and e.g. to renew tokens for user sessions.
JOC Identity Service Settings
The built-in Identity Service does not require any settings.
Shiro Identity Service Settings
The Shiro Identity Service does not require any settings.