...
- The Credential Store (CS) allows sensitive data to be encrypted and stored securely and independently of the application(s) such as YADE and the JobScheduler YADE JITL Jobs that use this data.
- The advantage of using a CS is that the CS stores sensitive information such as credentials in a standardized, secure and fully encrypted database and sensitive authentication information is not exposed in use. Applications access the CS database by using password, encryption-key file or a combination of both.
- The CS requires the use of a standard open database format (
.kdbor.kdbx), which allows the use of graphical and API interfaces across the most relevant operating systems.
Scope
This article describes a relatively simple example configuration to illustrate is in two parts:
- The first part describes the use of the Credential Store in a relatively simple example file transfer configuration. The
...
- configuration described can be used
...
- to transfer files from a live server and a download containing the configuration file is available so that users can get a working Credential Store up, running and
...
- tested as easily as possible.
This descriptions provided in this article also apply for the configuration of a settings file and Credential Store for use with the YADE instance that is integrated in the JobScheduler and available via the YADE JITL jobs. See the Using the Credential Store with the JobScheduler section below for more information.
Feature Summary
The Credential Store provides the following features:
- Compliance:
- All sensitive configuration information is encrypted.
- Access to the Credential Store can be securely protected by password, key file or password and key file.
"Password-free" authentication is possible. - Connection Authentication files such as public key files are used without being written to the file system.
- Management
- Configuration information can be centrally managed outside of a file transfer environment.
- Deployment
- The same file transfer configuration file can be used for development and production environments - only the Credential Store needs to be changed during deployment.
- Scope
- The Credential Store can be used for the following configuration information:
- file transfer source, target, proxy and jump host / DMZ,
- pre- and post-processing operations.
- The Credential Store can be used for file transfers carried out with both the YADE Client and the JobScheduler JADEJob and JADE4DMZJob JITL jobs.
- The Credential Store can be used for the following configuration information:
- Database Format and Applications
- The Credential Store uses the standard
.kdbor.kdbxopen database formats. A number of commercial and open source tools are available for configuring these database formats on a range of operating systems. These tools include KeePass 1.x, KeePass 2.x and KeePassX.
- The Credential Store uses the standard
...
The example presented in this article illustrates the configuration and use of the Credential Store in a simple file transfer operation that is carried out with the YADE Client.
...
- The second part of the article describes Credential Store configuration elements not covered by the example configuration. In addition, the use of the Credential Store in with the JobScheduler YADE JITL jobs is described
This article does not attempt to provide a step-by-step description of file transfer configuration, which is available elsewhere in this article, for example, in the tutorials for YADE and the JobScheduler.
| Anchor | ||||
|---|---|---|---|---|
|
The example presented in this article illustrates the configuration and use of the Credential Store as part of a simple file transfer operation - downloading files from an online server to the user's local file system.
The configuration is stored in an XML settings file and includes the elements specifying the Credential store and the file transfer as a whole. This settings file can be used by both the YADE Client and by the YADE JITL jobs that are provided with the JobScheduler.
The example described in this article is based on the simple file transfer example that is described in detail in The YADE Client Command Line Interface - Tutorial 1 - Getting Started article. This tutorial describes the configuration required to download a number of files from an online server provided by the SOS GmbH and save these files on the user's local file system. Using this server together with the downloaded configuration file means that users can get a working example up and running with a minimum of effort.
In the current example, the Credential Store is to store configuration information for the online server - i.e. for the file transfer source. The principle described can be equally well used for the configuration of multiple file transfer source, target, proxy and jump-host servers and for the other file transfer protocols that can be used by the YADE Client.
Note that a YADE Client or JobScheduler Master is required to carry out the example file transfer. Instructions for installing and configuring the YADE Client can be found in the YADE - Tutorials article. Instructions for installing and configuring the JobScheduler can be found in the JobScheduler Master - Installation Guide series of articles.
The example configuration file can be downloaded here:
...
Configuration Procedure for the Example
Installing the Credential Store
...
and configuring the KeePass database
KeePass 2, which is just one of the applications available for creating and configuring .kdb or .kdbx databases, has been used in the current article to implement the Credential Store database and is used in the screenshots. The installation and use of KeePass 2 is described on the KeePass Web Site.
Feature Availability
| Display feature availability | ||
|---|---|---|
|
The full range of Credential Store features such as secure, compliant and password-free use of the Credential Store as well as compatibility with KeePass .kdb databases requires the YADE Client in version 1.12.2 or newer.
Database Configuration
Credential Store databases are stored as either .kdb or .kdbx files on the file system.
The database included with the download files was configured as follows:
- Path:
.\jade_demo\keepass\demo_credential_store.kdbx - Master Password:
sos
Note that a Master Key file can be used to provide further protection for the database, either instead of or in addition to the Master Password. This is described in the Advanced Configuration section of this article below but has not been configured for the download database.
| Anchor | ||||
|---|---|---|---|---|
|
Connection configuration information is stored in the Credential Store as an Entry and Entries can be organized into Groups.
The following fields are available for storing information in a CS Entry:
- Title: The identifier for the Entry, this could be a string containing, for example, the host name/server name.
- User name: The user identification of a user account who is authenticated for the operation.
- Password: Assigned password for a user account or passphrase for a private key.
- URL: The host name/server name or IP address of the server.
- Notes: This block can be used to specify additional parameters for the file transfer.
- File Attachment & String Fields: Files such as PGP or SSH private keys can be stored as attachments.
- A first file is specified as an attachment .
- Further files are specified using String field parameter / value pairs.
YADE will retrieve the contents of an attached file at run-time - intermediate or temporary files are not created when reading attachments.
Note that Attachments and String Fields are specified in the KeePass GUI via the AdvancedEdit Entry tab.
The following information needs to be specified for the current example:
- Groups:
demo,ftp(optional) - Title:
demo_on_test.sos-berlin.com - User name:
demo - Password:
demo - URL:
test.sos-berlin.com(Alternatively, the IP address could have been specified here.)
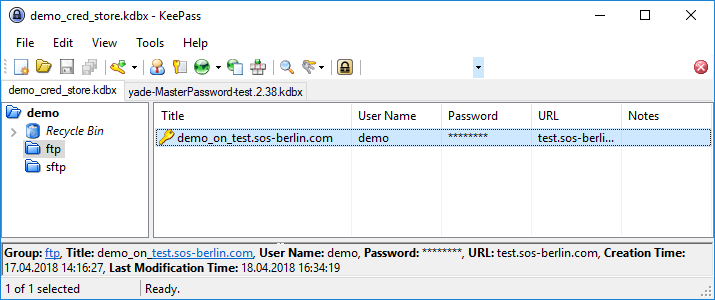
The following screenshot shows that two Groups have been configured for the current example, named "demo" and "ftp", along with the Entry "demo_on_test.sos-berlin.com".
The next screenshot shows the configuration of the parameters in the "demo_on_test.sos-berlin.com" Entry:
Integrating the Credential Store in a File Transfer Configuration
The use of the Credential Store is specified in YADE Client file transfer configuration files, which are written in XML. We recommend using the SOS XML Editor to edit these files. Instructions for downloading, installing and using the XML Editor are linked from this page.
In the remainder of the current article, it is assumed that readers have made themselves familiar with the organization of the YADE Client file transfer configurations into Profiles and Fragments. This is described in The YADE Client Command Line Interface - Tutorial 1 - Getting Started article mentioned above.
The current example uses the XML configuration from the Getting Started tutorial article above and describes the necessary configuration elements required to move the sensitive information such as user name and password from the XML file to the Credential Store. Users wishing implement the current example should download the tutorial file transfer configuration file linked above and open it in their XML Editor, where they can then add the necessary configuration information.
The information required to use the Credential Store falls into two "areas":
- Information about the Credential Store itself (location, how to access its contents, etc.).
This information is configured in the XML file in a CredentialStoreFragment. - Information about how the information in the Credential Store (server address, password, etc.) is to be accessed for the file transfer.
This information is stored as a string in each of the relevant XML ProtocolFragment child elements (Hostname, Account. etc.).
In addition, the ProtocolFragment element has a reference specifying that the Credential Store is to be used.
Specifying the Credential Store
The following list shows the organization of the XML elements required to specify the Credential Store. These elements and their attributes are shown in full in the XML Editor screenshot below.
FragmentsProtocolFragmentsFTPFragment name="ftp_demo_sos-berlin_cs"- ....
CredentialStoreFragmentRefref ="ftp_demo"
CredentialStoreFragmentsCredentialStoreFragmentname ="ftp_demo"CSFile file path%USERPROFILE%\jade_demo....CSAuthenticationPasswordAuthentication- etc.
CSEntryPath
Profiles- etc.
Addressing the information in the Credential Store
Parameters stored in a Credential Store database Entry can be addressed in the CredentialStoreFragment XML element as follows:
- The CSEntryPath element is used to specify the base path in the Credential Store database to the Entry.
In the current example this would be set to:demo/ftp/demo_on_test.sos-berlin.com
wheredemoandftpare (optional) Group names, as already mentioned, anddemo_on_test.sos-berlin.comis the Title of the KeePass database Entry.
The Credential Store Entry parameters are addressed using one of the following syntaxes:
- relative:
cs://@parameter_name, where the parameter_name is the name of the relevant parameter specified for the Entry - for example, url and the CSEntryPath element is filled as shown above
- fully specified:
cs://, and where the CSEntryPath element, which is a required element, is left blankdemo/ftp/@parameter_namedemo_on_test.sos-berlin.com
The following parameters are fully specified in the Credential Store in the current example:
- Hostname:
Note that a YADE Client is required to carry out the example file transfer. Instructions for installing and configuring the YADE Client can be found in the YADE - Tutorials article.
Configuration Procedure
Installing the Credential Store and configuring the KeePass database
KeePass 2 has been used in the current article to implement the Credential Store database. The installation and use of KeePass 2 is described on the KeePass Web Site.
Feature Availability
| Display feature availability | ||
|---|---|---|
|
The full range of Credential Store features such as secure, compliant and password-free use of the Credential Store as well as compatibility with KeePass .kdb databases requires the YADE Client in version 1.12.2 or newer.
Database Configuration
Credential Store databases are stored as either .kdb or .kdbx files on the file system.
For the examples described in the current article the following database was configured (on a Windows system):
- Path:
%USERPROFILE%\jade_demo\keepass\demo_cred_store.kdbx - Master Password:
sos
Note that a Master Key file can be used to provide further protection for the database. This is described in the Advanced Configuration section of this article below.
...
Connection configuration information is stored in the Credential Store as an Entry and Entries can be organized into Groups.
The following fields are available for storing information in a CS Entry:
- Title: The identifier for the Entry, this could be a string containing, for example, the host name/server name.
- User name: The user identification of a user account who is authenticated for the operation.
- Password: Assigned password for a user account or passphrase for a private key.
- URL: The host name/server name or IP address of the server.
- Notes: This block can be used to specify additional parameters for the file transfer.
- File Attachment & String Fields: Files such as PGP or SSH private keys can be stored as attachments.
- A first file is specified as an attachment .
- Further files are specified using String field parameter / value pair.
YADE will retrieve the contents of an attached file at run-time - intermediate or temporary files are not created when reading attachments.
Note that Attachments and String Fields are specified in the KeePass GUI via the AdvancedEdit Entry tab.
The following information needs to be specified for the current example:
- Groups:
demo,ftp(optional) - Title:
demo_on_test.sos-berlin.com - User name:
demo - Password:
demo - URL:
test.sos-berlin.com(Alternatively, the IP address could have been specified here.)
The following screenshot shows that two Groups have been configured for the current example, named "demo" and "ftp", along with the Entry "demo_on_test.sos-berlin.com".
The next screenshot shows the configuration of the parameters in the "demo_on_test.sos-berlin.com" Entry:
Integrating the Credential Store in a File Transfer Configuration
The use of the Credential Store is specified in YADE Client file transfer configuration files, which are written in XML. We recommend using the SOS XML Editor to edit these files. Instructions for downloading, installing and using the XML Editor are linked from this page.
In the remainder of the current article, it is assumed that readers have made themselves familiar with the organization of the YADE Client file transfer configurations into Profiles and Fragments. This is described in The YADE Client Command Line Interface - Tutorial 1 - Getting Started article mentioned above.
The current example uses the XML configuration from the Getting Started tutorial article above and describes the necessary configuration elements required to move the sensitive information such as user name and password from the XML file to the Credential Store. Users wishing implement the current example should download the tutorial file transfer configuration file linked above and open it in their XML Editor, where they can then add the necessary configuration information.
The information required to use the Credential Store falls into two "areas":
- Information about the Credential Store itself (location, how to access its contents, etc.).
This information is configured in the XML file in a CredentialStoreFragment. - Information about how the information in the Credential Store (server address, password, etc.) is to be accessed for the file transfer.
This information is stored as a string in each of the relevant XML ProtocolFragment child elements (Hostname, Account. etc.).
In addition, the ProtocolFragment element has a reference specifying that the Credential Store is to be used.
Specifying the Credential Store
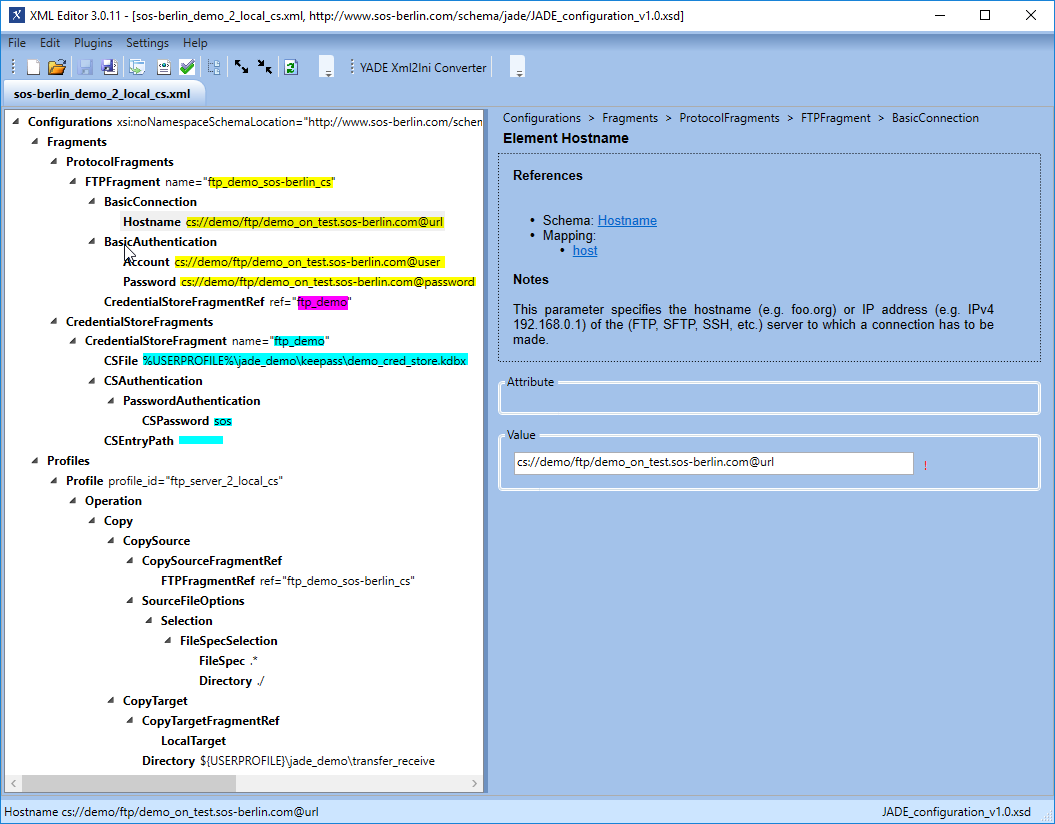
The following list shows the organization of the XML elements required to specify the Credential Store. These elements and their attributes are shown in full in the XML Editor screenshot below.
FragmentsProtocolFragmentsFTPFragment name="ftp_demo_sos-berlin_cs"- ....
CredentialStoreFragmentRefref ="ftp_demo"
CredentialStoreFragmentsCredentialStoreFragmentname ="ftp_demo"CSFile file path%USERPROFILE%\jade_demo....CSAuthenticationPasswordAuthentication- etc.
CSEntryPath
Profiles- etc.
Addressing the information in the Credential Store
Parameters stored in a Credential Store database Entry can be addressed in the CredentialStoreFragment XML element as follows:
- The CSEntryPath element is used to specify the base path in the Credential Store database to the Entry.
In the current example this would be set to:cs://demo/ftp/@urldemo_on_test.sos-berlin.com@urlspecifies the URL element stored in the database ) - Account:
wheredemoandftpare (optional) Group names, as already mentioned, andcs://demo/ftp/demo_on_test.sos-berlin.com
The Credential Store Entry parameters are addressed using one of the following syntaxes:
@user(where@userspecifies the User name element stored in the database)- Password:
- relative:
cs://@parameter_name, where the parameter_name is the name of the relevant parameter specified for the Entry - for example, url and the CSEntryPath element is filled as shown above
- fully specified:
cs://demo/ftp/demo_on_test.sos-berlin.com
The following parameters are fully specified in the Credential Store in the current example:
- Hostname:
cs://(wheredemo/ftp/@urldemo_on_test.sos-berlin.com@urlspecifies the URL element stored in the database ) - Account:
cs://demo/ftp/@userdemo_on_test.sos-berlin.com@userspecifies the User name element stored in the database) - Password:
cs://@passworddemo/ftp/demo_on_test.sos-berlin.com@passwordspecifies the Password element stored in the database)
Note that a full list of parameters is described in the Adding an Entry to the Credential Store section above.
Configuration in the XML Editor
| Info | ||
|---|---|---|
| ||
The XML Editor includes up-to-date documentation for elements as can be seen in the screenshot below, which shows the documentation for the Hostname element. |
The parts of the XML configuration relevant to the use of the Credential Store are shown in the following screenshot of the configuration for the current example, with parameter values highlighted according to their function:
The Transfer Target Directory
As can be seen in the screenshot above, the CopyTarget.Directory parameter is by default set for a Windows environment and set to:
${USERPROFILE}\jade_demo\transfer_receive
Depending on their operating system, users may find it necessary to modify this attribute before running the example.
XML Listing
The following code block can be opened to show the full XML configuration for the example:
@password(where@passwordspecifies the Password element stored in the database)
Note that a full list of parameters is described in the Adding an Entry to the Credential Store section above.
Configuration in the XML Editor
| Info | ||
|---|---|---|
| ||
The XML Editor includes up-to-date documentation for elements as can be seen in the screenshot below, which shows the documentation for the Hostname element. |
The parts of the XML configuration relevant to the use of the Credential Store are shown in the following screenshot of the configuration for the current example, with parameter values highlighted according to their function:
The Transfer Target Directory
The screenshot above shows a CopyTarget.Directory parameter for a Windows environment:
${USERPROFILE}\jade_demo\transfer_receive
Depending on their operating system, users may find it necessary to modify this attribute before running the example.
XML Listing
The following code block can be opened to show the full XML configuration for the example:
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
<?xml version="1.0" encoding="utf-8"?>
<Configurations xsi:noNamespaceSchemaLocation="http://www.sos-berlin.com/schema/jade/JADE_configuration_v1.0.xsd" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance">
<Fragments>
<ProtocolFragments>
<FTPFragment name="ftp_demo_sos-berlin_cs">
<BasicConnection>
<Hostname><![CDATA[cs://demo/ftp/demo_on_test.sos-berlin.com@url]]></Hostname>
</BasicConnection> | ||||||
| Code Block | ||||||
| ||||||
<?xml version="1.0" encoding="utf-8"?> <Configurations xsi:noNamespaceSchemaLocation="http://www.sos-berlin.com/schema/jade/JADE_configuration_v1.0.xsd" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"> <Fragments> <ProtocolFragments> <FTPFragment name="ftp_demo_sos-berlin_cs"> <BasicConnection><BasicAuthentication> <Hostname><<Account><![CDATA[cs://demo/ftp/demo_on_test.sos-berlin.com@urlcom@user]]></Hostname>Account> </BasicConnection> <BasicAuthentication> <Account><<Password><![CDATA[cs://demo/ftp/demo_on_test.sos-berlin.com@usercom@password]]></Account>Password> <Password><![CDATA[cs://demo/ftp/demo_on_test.sos-berlin.com@password]]></Password> </BasicAuthentication> </BasicAuthentication> <CredentialStoreFragmentRef ref="ftp_demo" /> </FTPFragment> </ProtocolFragments> <CredentialStoreFragments> <CredentialStoreFragment name="ftp_demo"> <CSFile><![CDATA[%USERPROFILE%\jade_demo\keepass\demo_cred_store.kdbx]]></CSFile> <CSAuthentication> <PasswordAuthentication> <CSPassword><![CDATA[sos]]></CSPassword> </PasswordAuthentication> </CSAuthentication> <CSEntryPath /> </CredentialStoreFragment> </CredentialStoreFragments> </Fragments> <Profiles> <Profile profile_id="ftp_server_2_local_cs"> <Operation> <Copy> <CopySource> <CopySourceFragmentRef> <FTPFragmentRef ref="ftp_demo_sos-berlin_cs" /> </CopySourceFragmentRef> <SourceFileOptions> <Selection> <FileSpecSelection> <FileSpec><![CDATA[.*]]></FileSpec> <Directory><![CDATA[./]]></Directory> </FileSpecSelection> </Selection> </SourceFileOptions> </CopySource> <CopyTarget> <CopyTargetFragmentRef> <LocalTarget /> </CopyTargetFragmentRef> <Directory><![CDATA[${USERPROFILE}\jade_demo\transfer_receive]]></Directory> </CopyTarget> </Copy> </Operation> </Operation> </Profile> </Profiles> </Configurations> |
Running the YADE Client with the Credential Store
The use of the Credential Store is contained within the settings file and is not exposed when calling the YADE Client. For example, on Windows systems, the YADE Client is called for the current example using:
...
| language | xml |
|---|---|
| title | Call on Windows systems |
...
</Profile>
</Profiles>
</Configurations> |
Running the YADE Client with the Credential Store
The use of the Credential Store is contained within the settings file and is not exposed when calling the YADE Client. For example, on Windows systems, the YADE Client is called for the current example using:
| Code Block | ||||
|---|---|---|---|---|
| ||||
C:\Program Files\sos-berlin.com\jade\client\bin>jade.cmd -settings="%USERPROFILE%\jade_demo\sos-berlin_demo_2_local_cs.xml" -profile="ftp_server_2_local_cs" |
After the YADE command has finished execution the number of files transferred can be read from the log file.
Note that the log files neither indicate that a credential store has been use for the transfer nor reveal any passwords.
| Show If | ||
|---|---|---|
| ||
Download ExampleA download is available containing a full XML configuration file for Windows users and Windows users with the necessary permissions will be able to use these files by unpacking the zip file to a Users of other operating systems may have to make minor configuration changes. |
| Anchor | ||||
|---|---|---|---|---|
|
Settings XML files such as the sos-berlin_demo_2_local_cs.xml
...
file which was used to configure the example described above can be used for JobScheduler JITL jobs. Here, only two parameters are needed to run the YADE JITL job (settings and profile) as can be seen in the next screenshot.
Note that we recommend that these parameters are set manually using the New button shown in the screenshot below and not using the Wizard button.
Note also that while the YADE Client runs under the current user account, the JobScheduler generally runs under a predefined account. This means that while paths in the configuration file can use parameters such as %USERPROFILE% when the configuration file is being used with the YADE Client, it is generally necessary to use absolute paths when the configuration file is to be used for JITL jobs.
After the YADE command has finished execution the number of files transferred can be read from the log file.
Note that the log files neither indicate that a credential store has been use for the transfer nor reveal any passwords.
Download Example
A download is available containing a full XML configuration file for Windows users and .kdbx database: jade_demo.zip
Windows users with the necessary permissions will be able to use these files by unpacking the zip file to a jade_demo folder in their User directory.
Users of other operating systems may have to make minor configuration changes.
...
The two parameters used to run the YADE JITL job (settings and profile) can be set for the YADE JITL jobs (JADEjob and JADE4DMZjob) as can be seen in the following screenshot.
Advanced Configuration
Key File Authentication
...
A first attachment for, for example, SSH would be configured in the XML settings file by specifying an AuthenticationFile element in the SSHAuthentication element.
...