| Table of Contents |
|---|
Introduction
...
Carry out the following steps:
- Set up the basic Basic LDAP configuration
- Set up the authentication
- Set up the authorization
- Defining the groupRolesMapping (optional)
- Defining the Roles per account in the
[users]section (optional) - Defining the search for groups
- Add Shiro settings
The Setup Procedure
Anchor
| Flowchart |
|---|
1 [label="1. Set up basic LDAP config\n(URL, etc)"] 1 -> 2 [weight=5, len=0.5] 2 [label="2. Set up authentication\n(userDnTemplate)"] 2 -> 3 3 [label="3. Set up authorization"] 3 -> 4 4 [shape="diamond", label="Are roles to be assigned \nwith groups from LDAP?",fillcolor="lightblue"] 4 -> 5 [label="Yes"] 5 [label="Define GroupRoles mapping"] 4 -> 10 [label="No"] 10 [label="Use Shiro to assign roles to accounts"] 10 -> E2 E2 [shape="circle", style="filled", label="End", color="pink"] 5 -> 6 6 [shape="diamond", label="Has account record a\nmemberOf attribute?",fillcolor="lightblue"] 6 -> 20 [label="Yes"] 20 [label="Specify User Search\l - searchBase\l - userSearchFilter"] 20 -> E3 E3 [shape="circle", style="filled", label="End", color="pink"] 6 -> 7 [label="No"] 7 [label="Specify Group Search\l - groupSearchBase\l - groupSearchFilter\l - groupNameAttribute"] 7 -> 8 8 [shape="diamond", label="Does member attribute contain\naccount name from login?",fillcolor="lightblue"] 8 -> E4 [label="Yes"] E4 [shape="circle", style="filled", label="End", color="pink"] 8 -> 9 [label="No"] 9 [label="Specify User Search\l - searchBase\l - userSearchFilter"] 9 -> E5 E5 [shape="circle", style="filled", label="End", color="pink"] |
| Anchor |
|---|
|
1. Basic LDAP Configuration
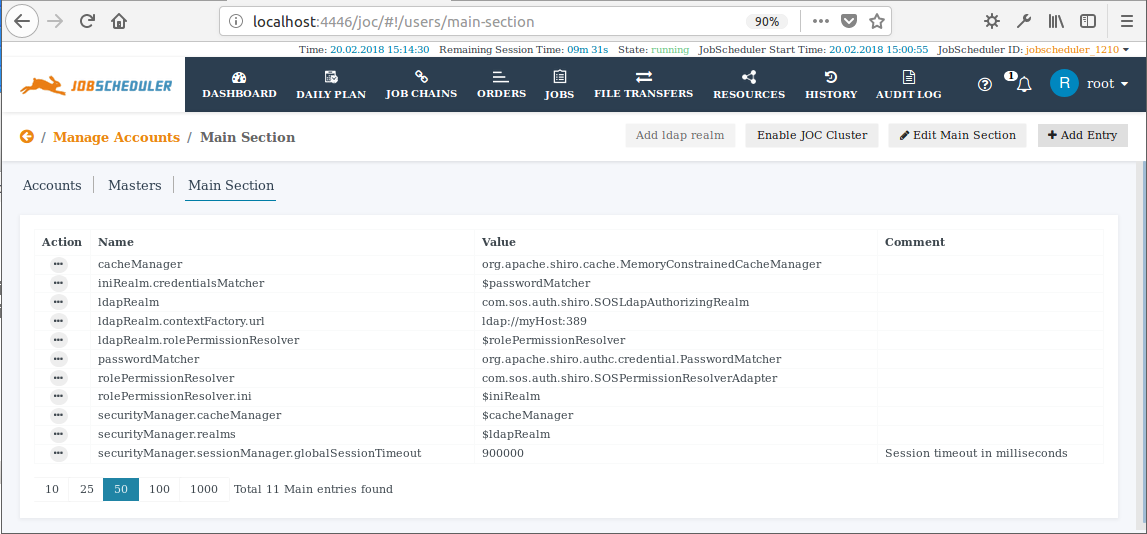
After setting up a Basic LDAP Configuration your LDAP is configured as part of the [main] section will look like this:of a Shiro configuration file. As already mentioned above this information can be added to the JOC Cockpit either by adding it to a shiro.ini file or by using the editor in the Main Section of the JOC Cockpit Manage Accounts view (in Version 1.12.1 and newer).
A Basic LDAP configuration in the [main] section will contain the following elements, with the ldapRealm.contextFactory.url being modified to suit the LDAP server being used:
| Code Block | ||||
|---|---|---|---|---|
| ||||
[main]
rolePermissionResolver | ||||
| Code Block | ||||
| ||||
[main] ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealmSOSPermissionResolverAdapter ldapRealmrolePermissionResolver.contextFactory.urlini = ldap://myHost:389 $iniRealm rolePermissionResolverldapRealm = com.sos.auth.shiro.SOSPermissionResolverAdapterSOSLdapAuthorizingRealm rolePermissionResolverldapRealm.contextFactory.iniurl = $iniRealmldap://myHost:389 ldapRealm.rolePermissionResolver = $rolePermissionResolver securityManager.realms = $ldapRealm cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager securityManager.cacheManager = $cacheManager |
An Add LDAP realm function is available in the Main Section of the JOC Cockpit Manage Accounts view that adds the above Basic LDAP configuration in a single step. Both the button used to activate this function and the configuration items added can be seen in the screenshot below.
| Info | ||
|---|---|---|
| ||
Note that the Administrators wishing to use a are therefore recommended to modify the securityManager element immediately to:
|
The following table lists the basic items used to configure an LDAP realmThe following table lists the basic items used to configure an LDAP realm. These items are configured in the [main] section of the shiro.ini file and cannot be changed with the Account Management in JOC Cockpit.
(See the Authentication and Authorization - Configuration article for more information about the shiro.ini file)
...