Diagram
These options apply to the handling of files on a source server. They specify e.g. the Selection of files for Copy and Move operations. A file Selection includes specifying one of In some file transfer scenarios the recipient of a file does not know when the sender creates the file. In case of (very) large files the recipient may try to read the file before the sender has finished writing it. This can result in the recipient retrieving an incomplete file. Including the CheckSteadyState parameter ensures that the file is checked at its reception point for completeness before starting the transfer. Including the CheckSteadyState parameter ensures that the file is checked at its reception point for completeness before starting the transfer. If the check of the steady state of one incoming file did not succeed successfully then no file will be transferred. Note that this is not a very reliable approach as the recipient checks the date of last modification and the size of the file. If neither changes during a specified a period of time then the file is assumed to be complete. However, if transmission is terminated without the file being completely written, the network goes down or the processing speed of the file is slow, then the receiver will get a corrupted file. The shorter the check interval is chosen the more likely it may happen that a file is detected as steady, although this was not yet finished writing. Directives are options that specify the behavior with specific file characteristics: Polling is the YADE capability to wait for incoming files. This parameter specifies the maximum number of files that are considered for transfer. If additional files were available then they will be ignored. Note that it is not possible to specify which files will be ignored should the value set for this parameter be exceeded. It therefore only makes sense to use this parameter in particular situations such as when the contents of a directory will be repeatedly polled. This parameter makes use of a checksum file that is available with the source of a file transfer. The name of the checksum file is assumed to be the same as the source file with an additional extension .md5. During file transfer the contents of the checksum file is compared with the checksum that is calculated from the transfer of the file. When used with a jump host then integrity checking applies to source and jump host, not to the target of the transfer. With this element being used a checksum file is expected on the source system and the integrity hash for the target file is calculated and compared with the respective integrity hash of the source file. If the hashes are not equal then the file transfer will be rolled back. If the checksum file on the source system is missing then this will be reported as an information but will not affect the transfer of files. 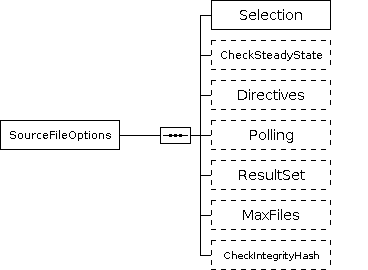
SourceFileOptions
Notes
Element
Type
Required
Description
Selection
Required
CheckSteadyState
Optional
Notes
Directives
Optional
Notes
Polling
Optional
ResultSet
Optional
MaxFiles
int
Optional
CheckIntegrityHash
Optional
Notes
References
References Notes
References
References
References Notes
References Notes
References
Overview
Content Tools