Introduction
Role based access management is offered from JS7 - Identity Services within the scope of JS7 - Identity and Access Management.
- The Identity Service Type determines if roles are managed from JOC Cockpit or from the Identity Provider, for example from an LDAP Server.
- The JS7 - JOC Identity Service provides the management of roles.
- The JS7 - HashiCorp® Vault Identity Service provides management of roles if the
VAULTIdentity Service Type is used.
- Permissions are managed from JOC Cockpit independently of the Identity Service in use.
- For the assignment of roles to user accounts see the JS7 - Manage User Accounts article.
Roles and Permissions
Role based Access Management
User accounts are assigned a number of roles.
- Each role is assigned a number of permissions.
- Permissions are available in the following flavors:
- Additive Permissions are granted to a user account and add to the permission set of a user account.
- Subtractive Permissions deny use of a permission and restrict the user account's permission set as they beat Additive Permissions across roles.
- Users are free to create any roles and to assign permissions. Roles are frequently determined from an organizational point of view, for example:
- administrator
- application manager
- business user
- JS7 ships with a number of defaults for roles and permissions, see the JS7 - Default Roles and Permissions for details.
Please keep in mind that at least one role that includes administrative permissions to access all objects in JOC Cockpit and Controllers is required and has to be assigned an administrative user account. If all administrative roles are deleted, then this corresponds to locking the door behind you and throwing away the keys. In this situation refer to the JS7 - Rescue in case of lost access to JOC Cockpit article.
Scope and Structure of Permissions
Permissions can be specified in scope and hierarchy:
- Scope
- JOC Cockpit Permissions are assigned for operations in JOC Cockpit, for example, for managing calendars and the daily plan etc.
- Controller Permissions are assigned for operations on scheduling objects per Controller, for example, for deploying workflows, adding orders etc.
- If more than one Controller is connected to JOC Cockpit then a user account can be assigned a role that for example allows deployment to one Controller but not to other Controllers.
- Controller permissions can be specified as a default for all Controllers and they can be specified on an individual Controller basis.
- Permission Tree
- Permissions can be considered as a tree that offers a hierarchy of branches.
- Granting or denying permissions at a higher level inherits the permission assignment recursively to deeper levels of the tree.
- Permission Status
- Permissions can take one of three status values, being unassigned, granted or denied.
- Unassigned permissions do not suggest any assumption if the permission is granted or denied.
- Granted permissions are considered additive within limits as they can be overruled by denied permissions.
- Denied permissions are considered subtractive without limits as they cannot be overruled by granted permissions.
- Permission Sets
- Roles are assigned permissions. A user account can accumulate a number of roles, therefore permissions are merged to a permission set by the following rules.
- JOC Cockpit Permissions
- Unassigned permissions are ignored.
- Granted permissions work across any roles unless merged with a denied permission from a role.
- Denied permissions work across any roles and cannot be overruled by granted permissions from any role.
- Controller Permissions
- Default Controller
- Unassigned permissions are ignored.
- Granted permissions overrule unassigned permissions from any roles and Controllers.
- Granted permissions can be overruled from all roles. They can be:
- denied by a permission of the Default Controller specified by another role,
- denied by a permission for a Specific Controller.
- Denied permissions
- Specific Controller
- Unassigned permissions are ignored, instead the permissions of the Default Controller are applied.
- Granted permissions work across all roles unless denied by a permission from a role for the given Controller.
- Denied permissions work without limits across all roles for the given Controller.
- Default Controller
- JOC Cockpit Permissions
- Roles are assigned permissions. A user account can accumulate a number of roles, therefore permissions are merged to a permission set by the following rules.
Views
Views are available for roles and permissions including the Graphical Permissions View and the Textual Permissions View.
Roles View
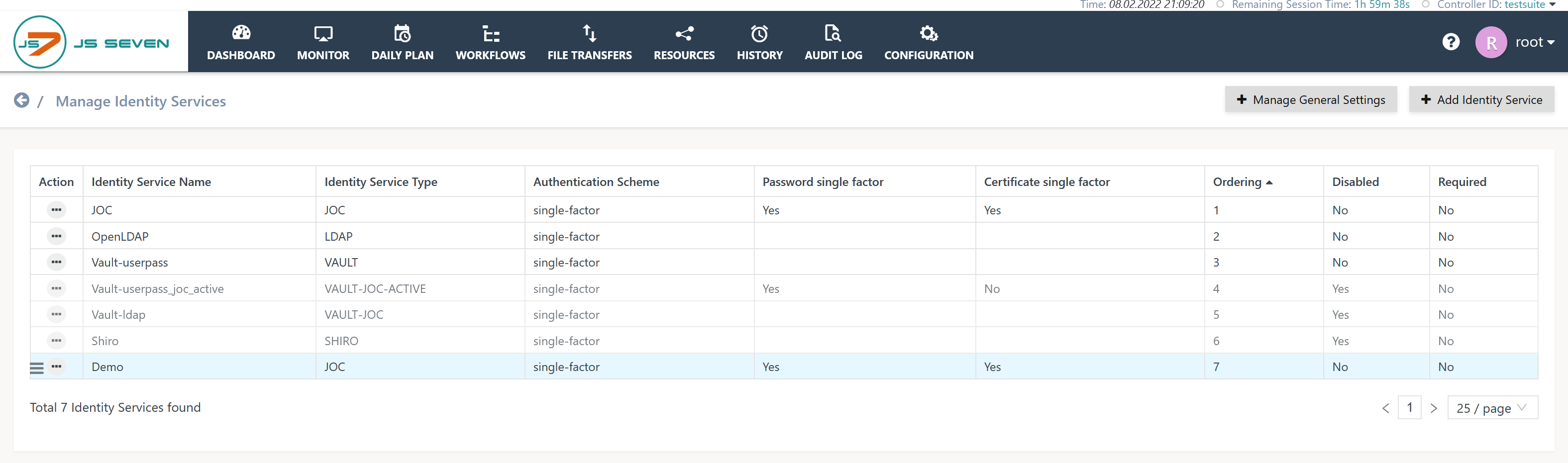
Users can click the name of an Identity Service from the list of Identity Services:
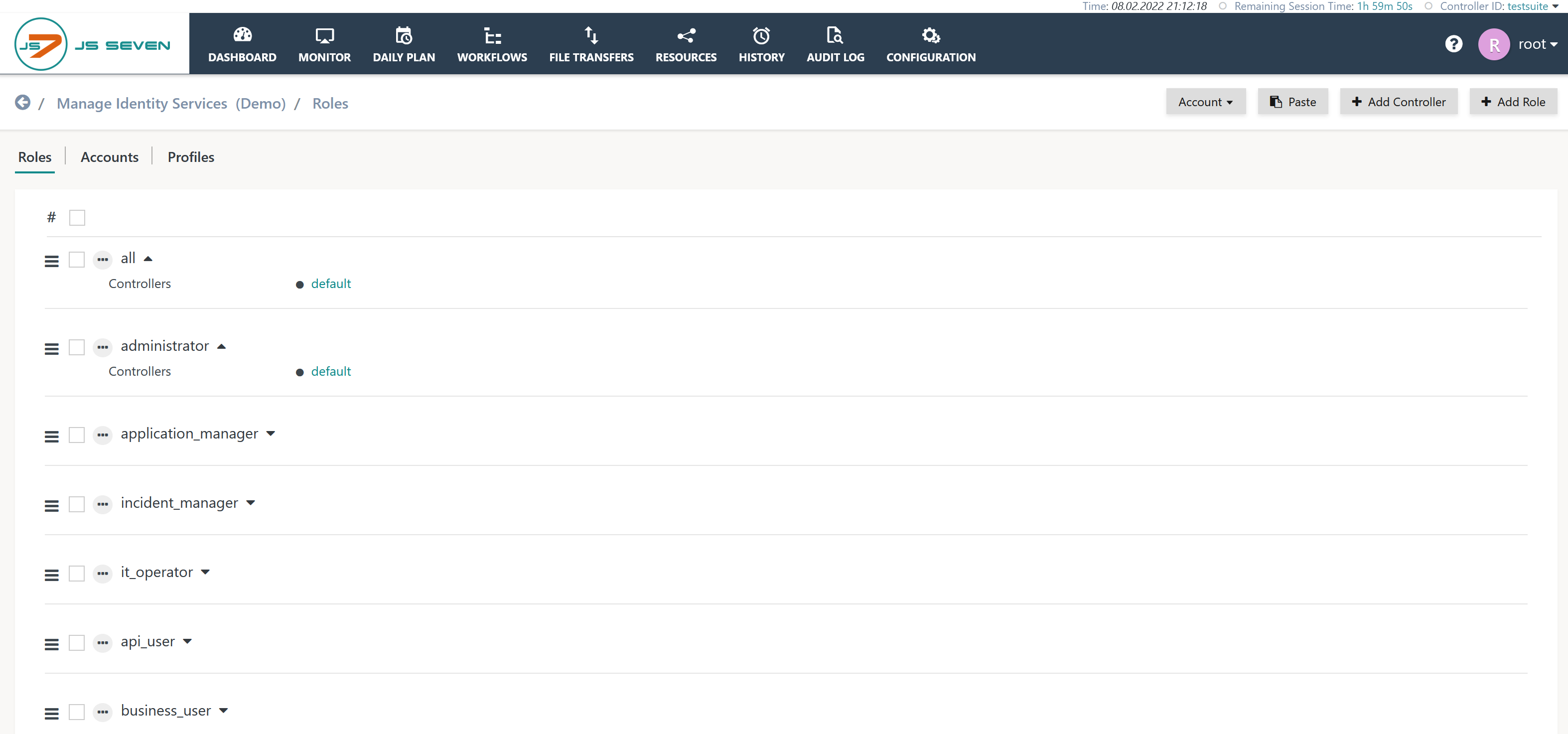
Having selected an Identity Service the Roles view is displayed like this:
A default link is available for each role to navigate to the Graphical Permissions View.
Additional links can be added by use of the Add Controller button. Such links are used to Assign Permissions for a Specific Controller.
Graphical Permissions View
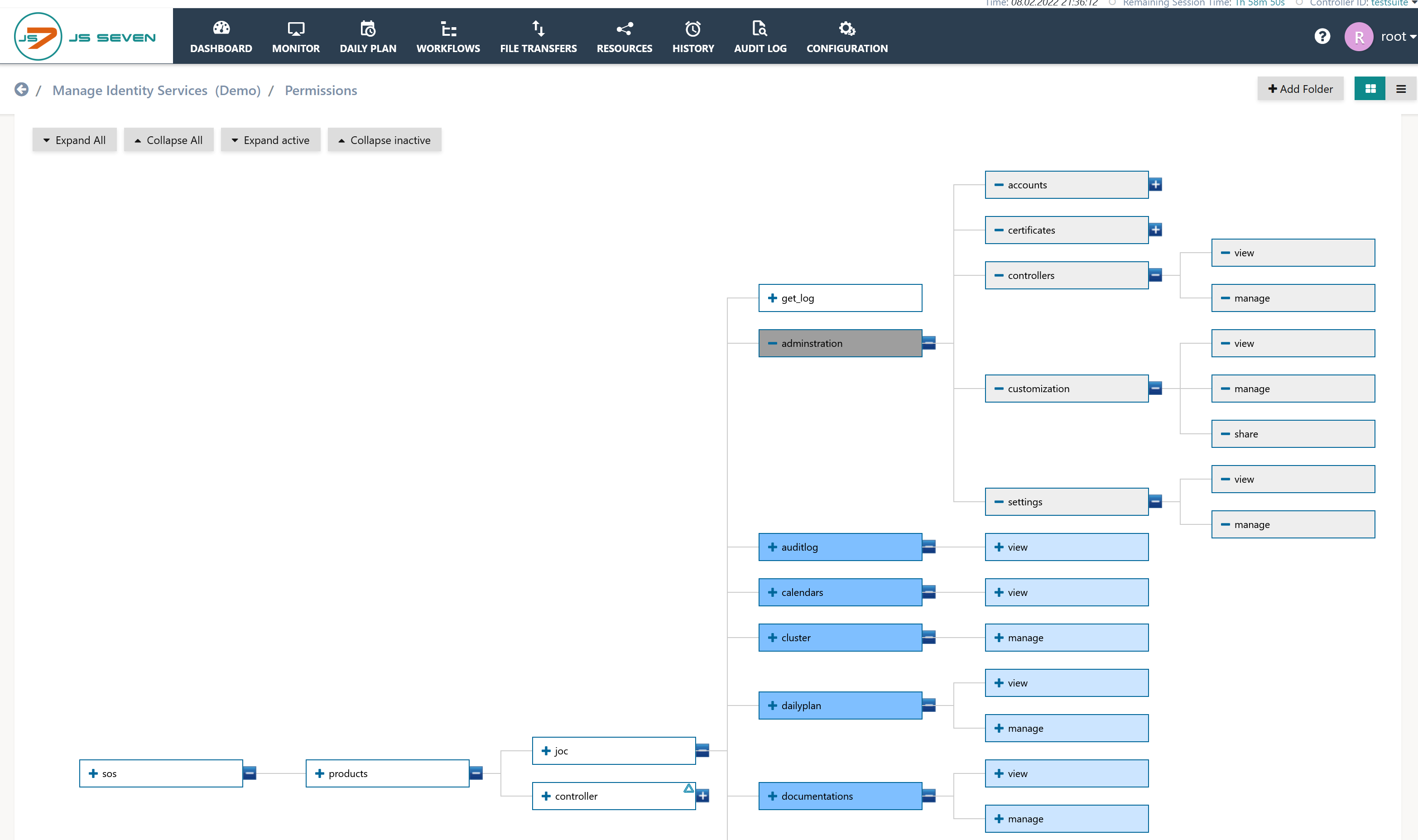
The view allows graphical navigation and selection of permissions and is the default view for the permissions of a given role:
- Explanation:
- Navigation
- The Expand All and Collapse All buttons open and close any child branches.
- The Expand Active and Collapse Active buttons open and close child branches with granted or denied permissions.
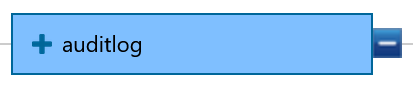
- The
+and-icons at the right edge of each permission icon open and close child branches.
- Status and Colors
- Permissions show the following background colors to indicate the status:
- White: Permission is not assigned, i.e. is neither granted nor denied.
- Dark Blue: Permission is granted and the grant is inherited to child permissions recursively.
- Light Blue: Permission is inherited from a granted parent permission.
- Dark Grey: Permission is denied and the denial is inherited to child permissions recursively..
- Light Grey: Permission is inherited from a denied parent permission.
- Display of permission can include a triangular attention sign such as
- The white background color indicates an unassigned permission, the triangle indicates that further down in the permission hierarchy a permission is granted or denied.
- The blue background color indicates a granted/inherited permission, the triangle indicates that further down in the permission hierarchy a permission is not granted or is denied.
- Granting Permissions
- Clicking the middle of an unassigned (white) permission grants the permission (dark blue).
- Clicking the middle of a granted permission revokes the grant and puts the permission to the unassigned status (white).
- Denying Permissions
- The
+icon inside a permission icon denies the permission (dark grey) recursively for child permissions that are located deeper in the permissions tree (light grey). - A denied permission shows the
-icon, clicking this icon revokes the denial and puts the permission to the unassigned status.
- The
- Permissions show the following background colors to indicate the status:
- Undo/Redo
- Changes to the permissions tree are stored in the JS7 - Database.
- The Undo button allows the last 10 changes to be undone stepwise.
- Any changes held in the Undo button will be deleted when the user leaves the Permissions sub-view.
- The Redo button changes the permissions tree back to its initial state when the Permissions sub-view is displayed.
- The status held with the Redo button is deleted when a user leaves the Permissions sub-view.
- Navigation
Textual Permissions View
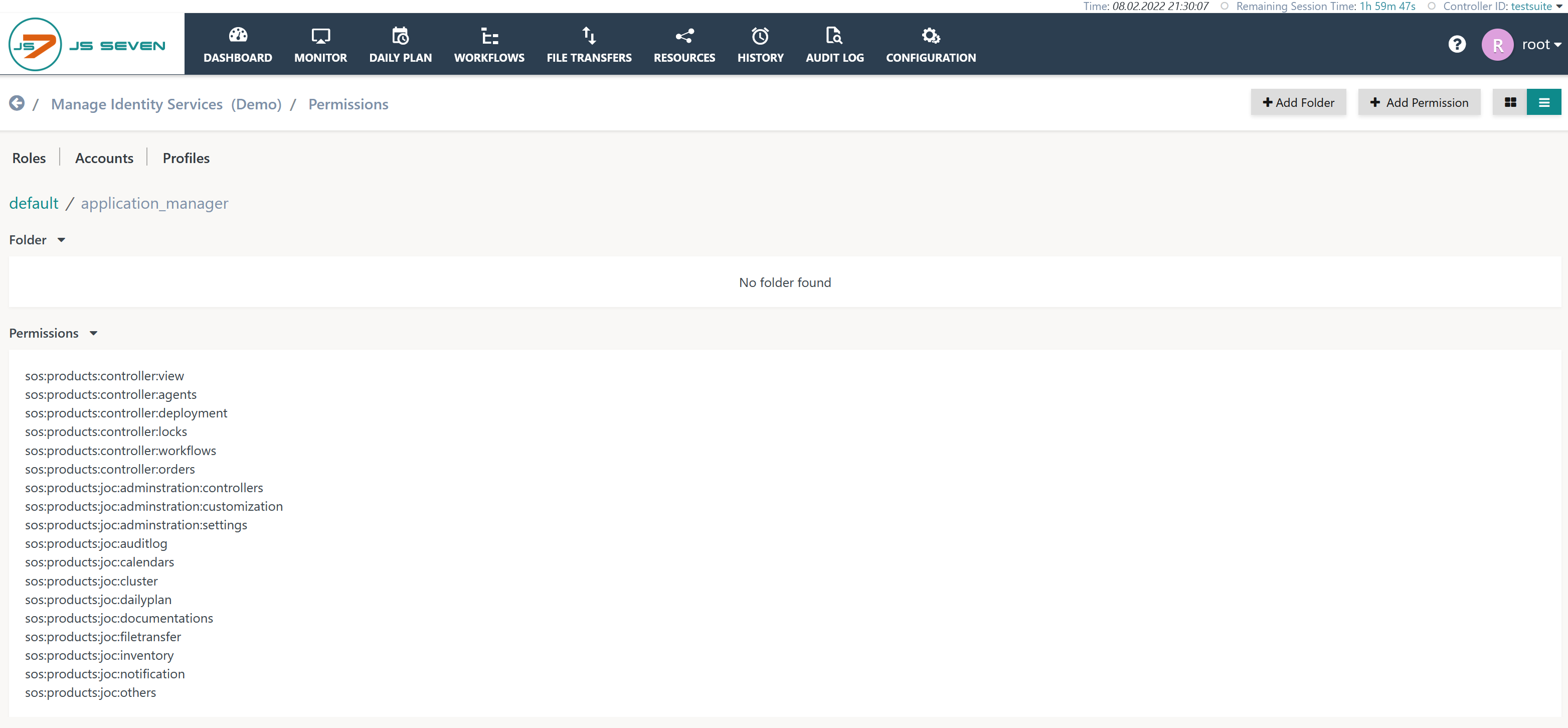
The view acts as an alternative to the Graphical Permissions View and displays permissions from a list of textual entries.
The right upper corner of the Permissions sub-view allows the user to toggle between the Graphical and Textual Permissions Views.
- Explanation:
- Individual permissions can be modified and can be removed from a role using the pencil icon and X icon, which are faded in when the user's mouse is moved over a permission.
- The Edit function allows the permission to be made subtractive, i.e. for permissions granted at a higher level the selected permission and any child permissions are denied.
- The folder part of the view is used to restrict the role to access particular folders only - this includes any scheduling objects such as workflows which are only visible from the assigned folder.
Assignment Strategies
Permission Hierarchy
Permissions are organized in a hierarchical way:
- A role with the permission
sos:products:controller:viewallows a user to view Controllers only, while a user with thesos:products:controllerpermission is able to carry out any operations such as view, restart, terminate, and to switch-over between Controller instances. - The JS7 - Permissions article explains the list of permissions.
Permission Assignment
Assign specific Permissions only
Consider a user account being assigned an application_manager role holding the following permission:
sos:products:controller:view
This permission does not allow the application_manager role to perform any modifying operations on Controllers. Instead, such permissions are granted individually by using:
sos:products:controller:restartsos:products:controller:terminate
Assign global Permissions, Deny specific Permissions
The following permissions allow the application_manager role to view and to restart a Controller, but not to terminate a Controller and not to switch-over between Controller instances:
sos:products:controller:viewsos:products:controller:restart
Alternatively, users might prefer to grant the role a higher level of permissions and then to deny one or more specific permissions. This approach is used for example with the following permission set:
sos:products:controller-sos:products:controller:switch_over
The sos:products:controller permission is an overall Controller permission including permissions to view, restart and terminate a Controller. The -sos:products:controller:switch_over permission is denied.
Minimum Permission Assignment
User accounts have to be assigned a role with the following minimum permission set in order to be able to login to the JOC Cockpit:
sos:products:joc:administration:controller:view
Assignment Operations
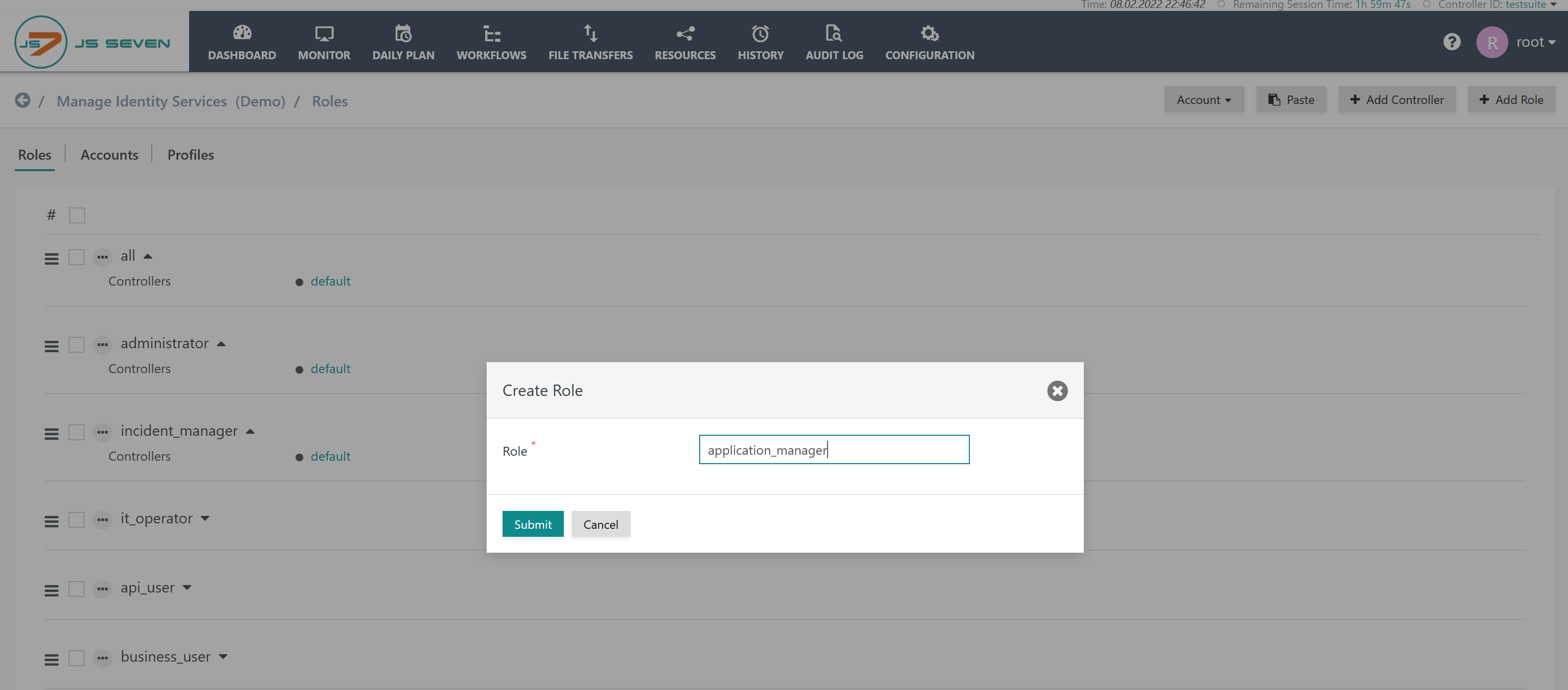
Add Role
A role can be added from the Roles view by use of the Add Role button like this:
Add Permissions
Graphical Permissions View
Permissions are added by clicking the relevant permission icon in the Graphical Permissions View:
Unassigned Permissions
The white background color indicates that a permission is not assigned, i.e. is not granted and it is not denied.
Clicking the middle of an unassigned (white) permission grants the permission (dark blue).
Granted Permissions
A dark blue background color indicates that a permission is granted and that the grant is inherited to child permissions recursively.
Clicking the middle of a granted permission revokes the grant and puts the permission to the unassigned status (white).
Denied Permissions
The dark grey background color indicates that a permission is denied and that the denial is inherited to child permissions recursively..
Clicking the - of a denied permission revokes the denial and makes it a granted permission (dark blue). Clicking once again makes it an unassigned permission (white).
Textual Permissions View
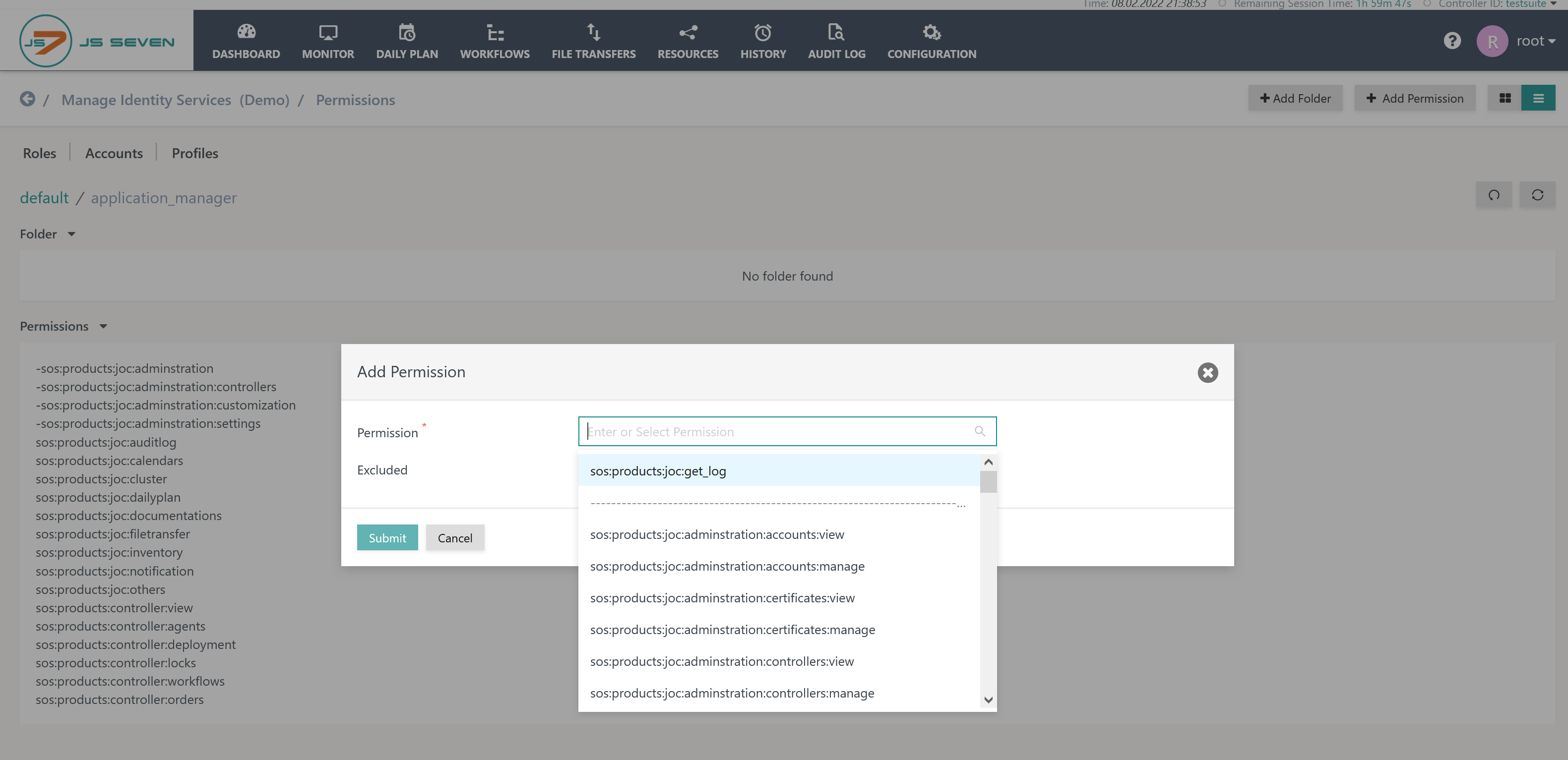
The Add Permission button in the Permissions sub-view allows selection of permissions from a list as described below.
- Note that specific permissions are used from a list. Users can modify permissions to have a more global or more specific scope.
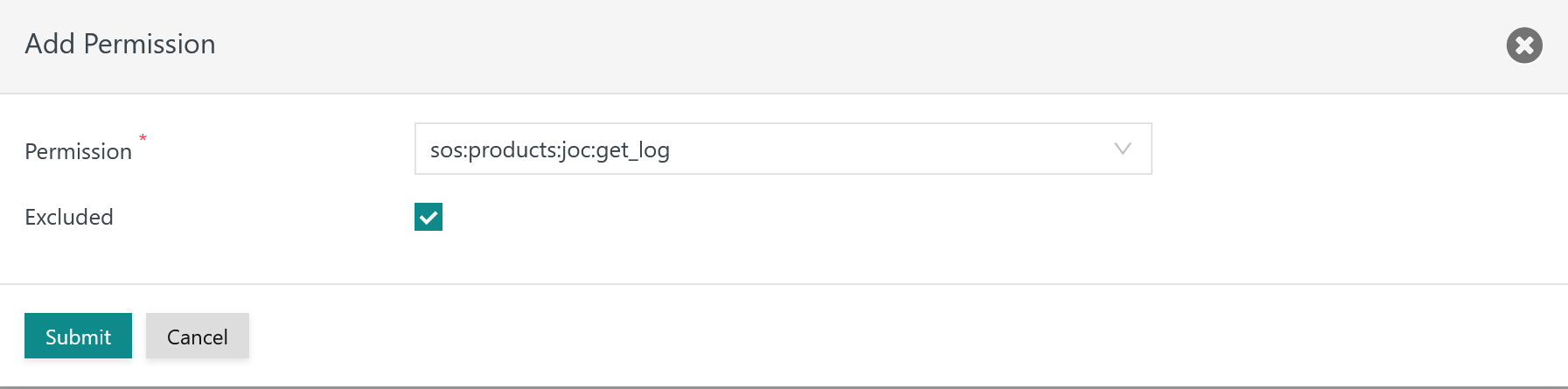
- For example, in the screenshot below, the
sos:products:joc:get_logpermission is assigned: - Additive Permissions: by default selected permissions are granted, i.e. they are added to the role's permission set.
- Subtractive Permissions: selected permissions are denied by removing a specific part of a more global permission. This is achieved by use of the Excluded checkbox.
- For example, in the screenshot below, the
Modify Permissions
Graphical Permissions View
See the instructions provide above about how to Add Permissions.
Textual Permissions View
Permissions can be modified by moving the mouse to one of the permissions displayed:
When the mouse is hovering the permission then the following editing icons are displayed:
Explanation:
- The pencil icon is displayed to offer modification of the permission.
- The X icon can be used to remove a permission from a role.
- Note that a role must be configured to be assigned either a permission or a folder as otherwise the role is considered empty and will be deleted.
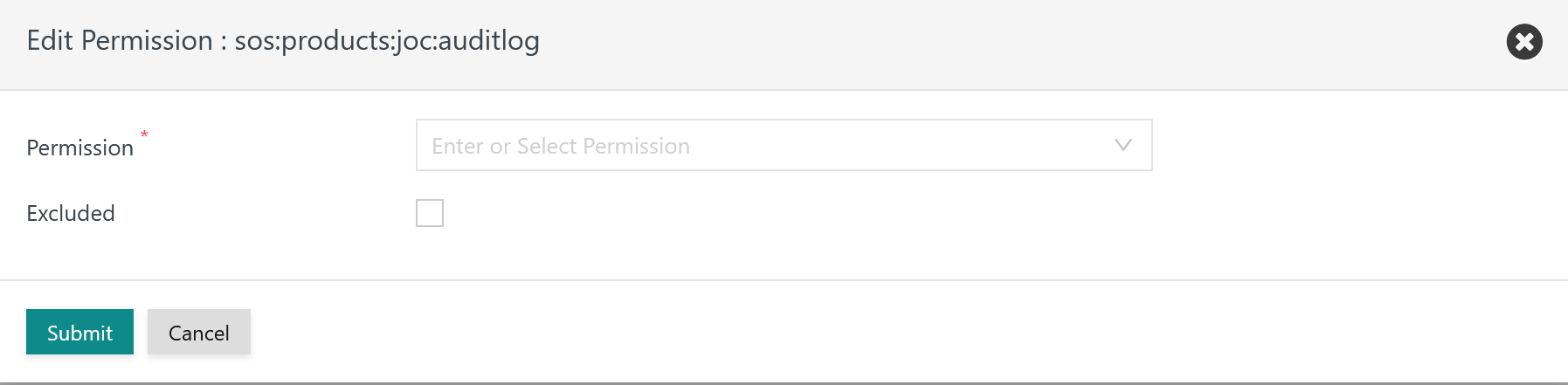
When clicking the pencil icon then the following popup window opens:
This allows the permission to be switched or be made an Additive Permission or Subtractive Permission depending on the Excluded checkbox.
Assign Permissions for a Specific Controller
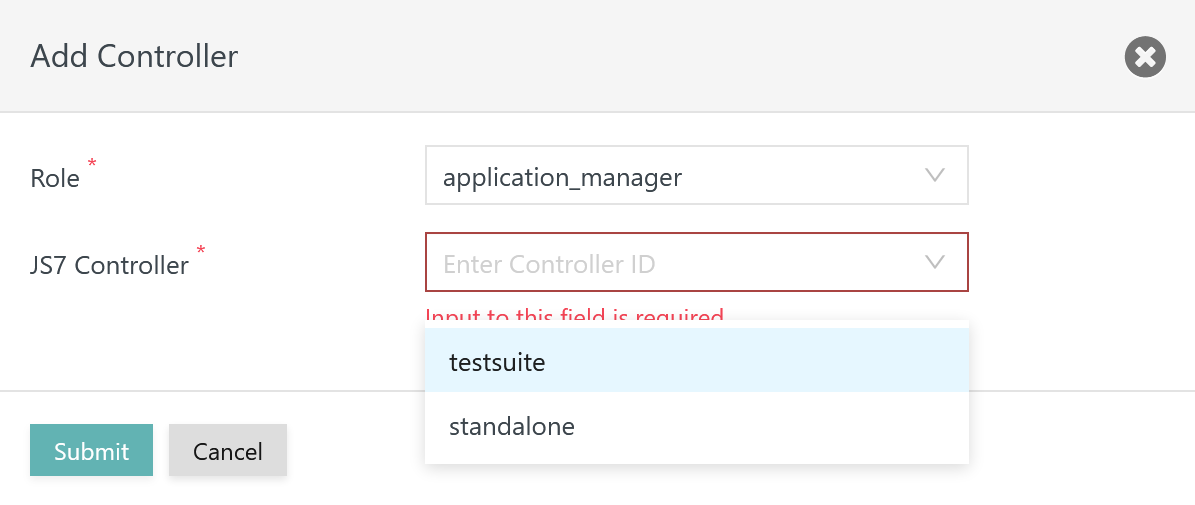
By default user accounts are granted permissions for any Controllers registered with JOC Cockpit. Permissions that should be applicable to a Specific Controller only can be added to a role. This can be achieved from the Roles view:
In the above screenshot, the application_manager role is assigned a Specific Controller with ID testsuite.
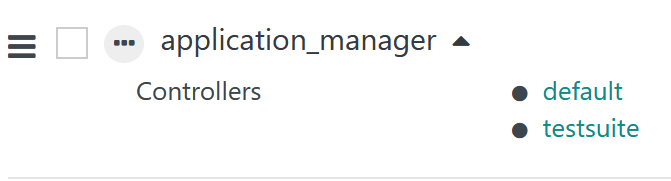
When the testsuite Controller is selected the role displays two links for default Controller and for the testsuite Controllers like this:
In this configuration, the application_manager role is not granted any permissions specific to the Controller ID testsuite. A minimum of one permission has to be added:
- Default Permissions:
sos:products:controller:view
- Permissions for a Specific Controller such as
testsuite:sos:products:controller:agents:view
The JS7 - Dashboard allows switching between connected Controllers and the display of the status of Agents registered with the respective Controller. This requires that the view permission described above for the Controller is in place.
Assign Folder Permissions
Inventory folders can be used to restrict access to objects such as workflows and schedules. For example, user accounts can be restricted to access objects for particular mandators / clients only.
By default permissions are granted for all folders. However, roles can limit access to specific folders.
This is achieved by adding folder permissions, i.e. a set of permissions to view only the content of a specific folder. With folder permissions in place the permission to access any other folders is automatically denied. Should folder permissions be applied to a number of folders then each folder has to be added individually for the given role.
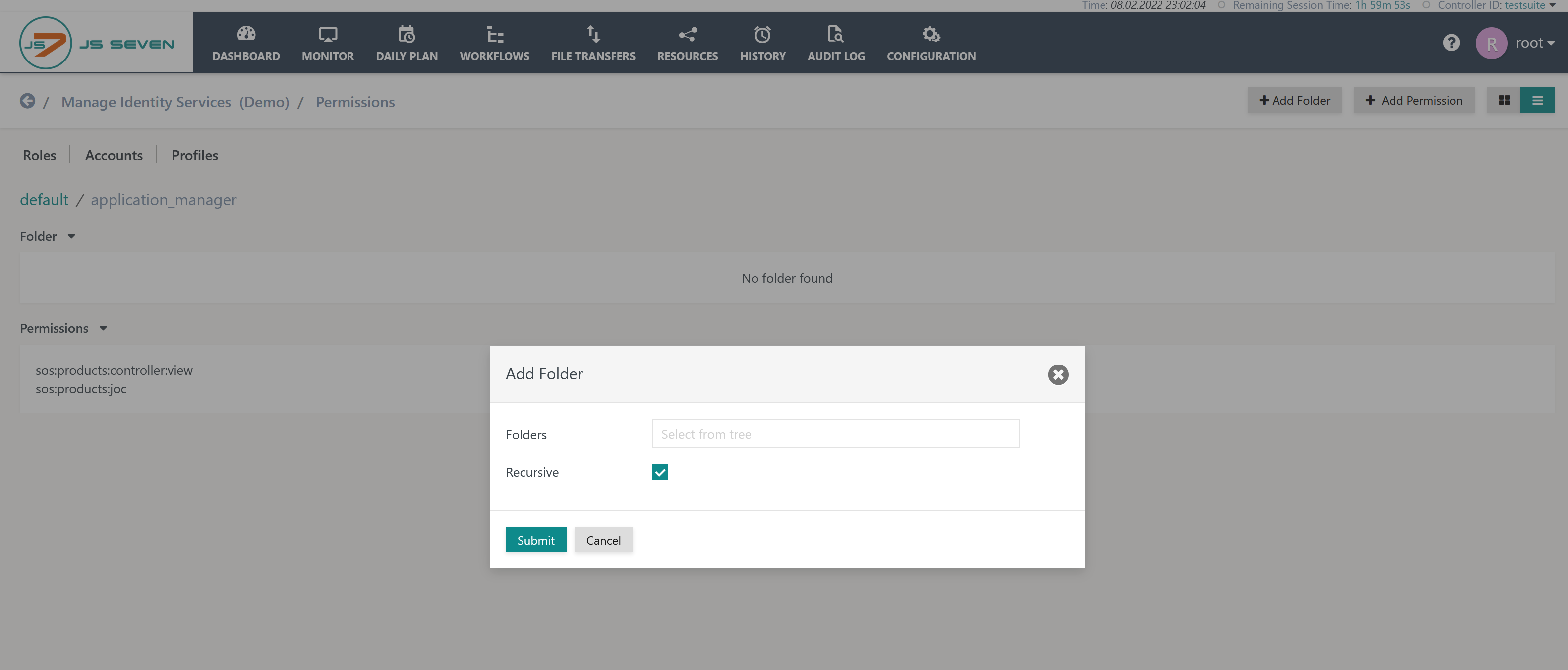
Add Folder
Inventory folders are added by use of the Add Folder button visible in the upper right corner of both the Graphical Permissions View and the Textual Permissions View for the relevant role like this :
Explanation:
- Folders are selected from a tree widget that is opened by clicking the folder input field.
- The Recursive option grants access to any sub-folders of the selected inventory folder.