Page History
...
The following integration level is available from the OIDC Identity Service Type:
| Identity Service | Identity Service Configuration Items | ||||
|---|---|---|---|---|---|
| Service Type | Built-in | User Accounts/Passwords stored with | User Accounts/Passwords managed by | Roles/Permissions stored with | Roles->User Accounts Mapping managed with |
| OIDC-JOC | yes | OIDC Identity Provider | OIDC Identity Provider | JS7 Database | JOC Cockpit |
| OIDC | yes | OIDC Identity Provider | OIDC Identity Provider | OIDC Identity Provider | JOC Cockpit |
Explanation:
- Service Type:
OIDC-JOC- Management of user accounts with passwords is performed by the OIDC Identity Provider
- The assignment of roles to user accounts is performed by the JOC Cockpit Application.
- This is provided by the Accounts View where the a the roles are assigned to the known accounts .
- The JOC Cockpit stores user accounts and role assignments: in the JS7 - Database.
- The JOC Cockpit does not know passwords of user accounts or the access tokens of successful authentication.
- Service Type:
OIDC- Management of user accounts with passwords is performed by the OIDC Identity Provider
- The assignment of roles to user accounts is performed by the JOC Cockpit Application.
- The accounts view is not provided when using OIDC
- The assignment of roles to accounts is provided by the group roles mapping editor in the "Manage Settings View" of the OIDC Identity Service.
- The JOC Cockpit does not store user accounts and role assignments. This is done by the the OIDC Identity Provider
- The JOC Cockpit does not know passwords of user accounts or the access tokens of successful authentication.
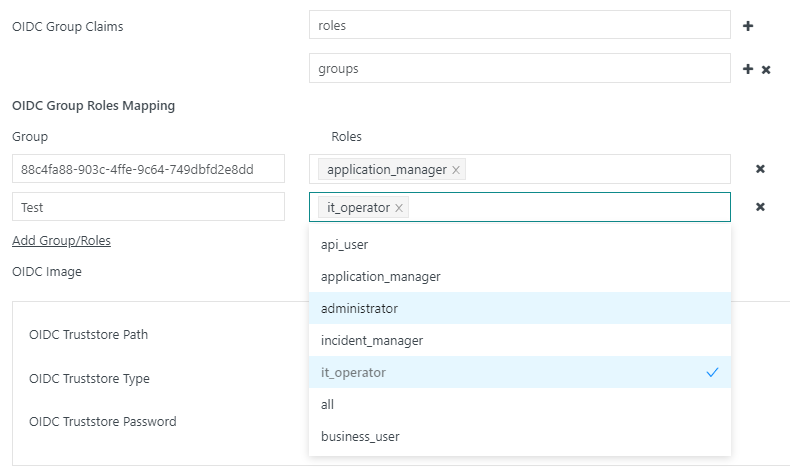
Group roles mapping
Roles are assigned to accounts via the editor for assigning group roles in the "Manage settings" view of the OIDC identity service.
A list of claims containing the groups configured in the OIDC provider can be defined. The available claims can be checked by checking the JW token during registration.
During assignment, the groups from the OIDC provider are assigned to the roles defined in the identity service. Any number of roles can be assigned to each group.
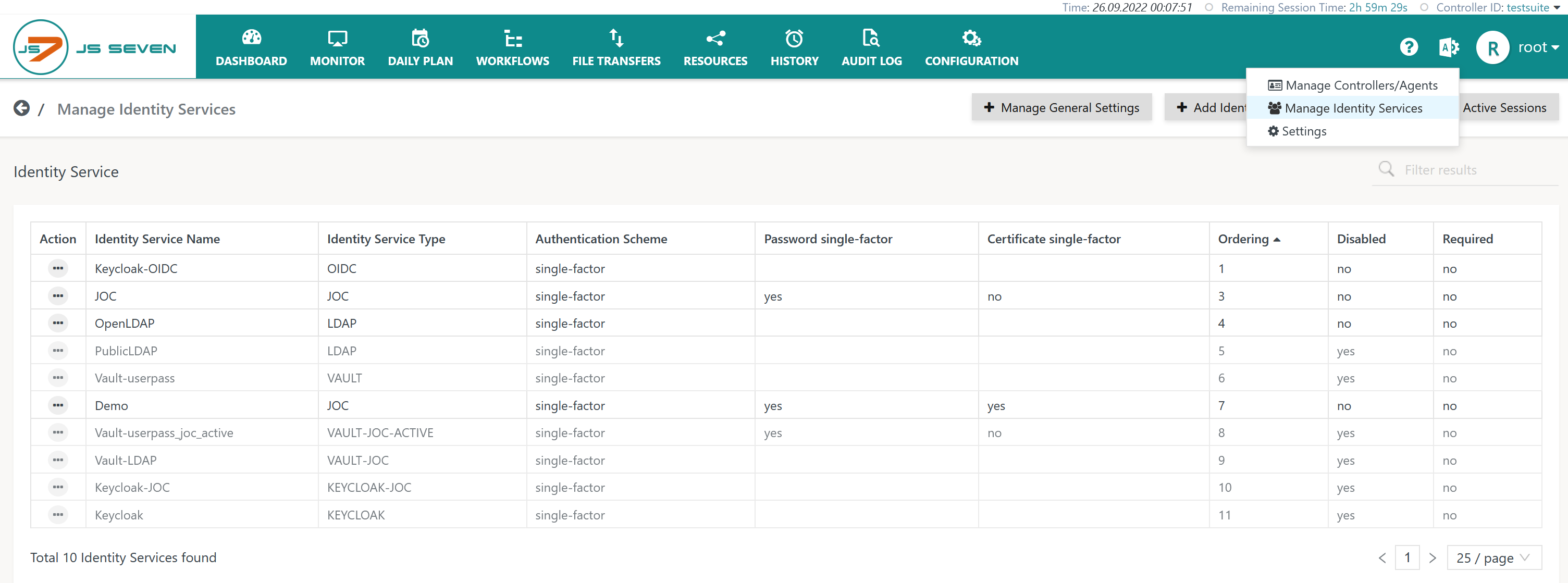
Identity Service Configuration
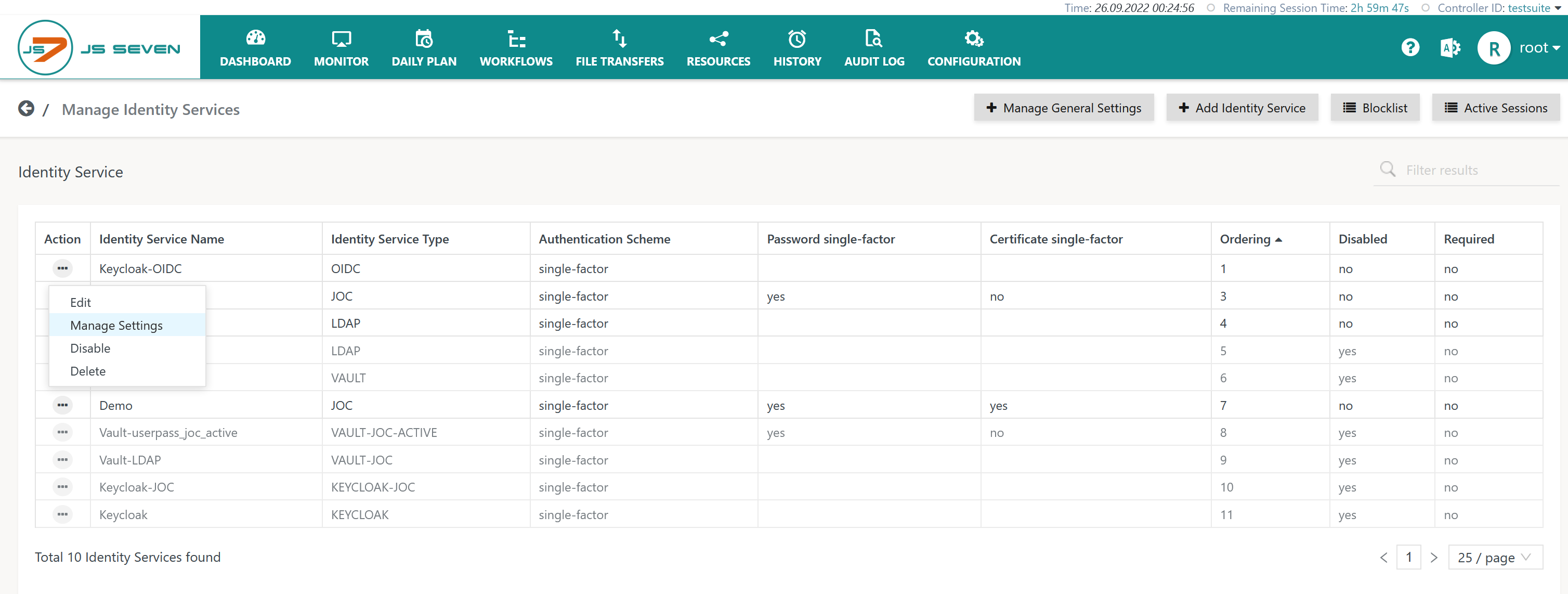
The icon in the JOC Cockpit main menu is used to select the Manage Identity Services page:
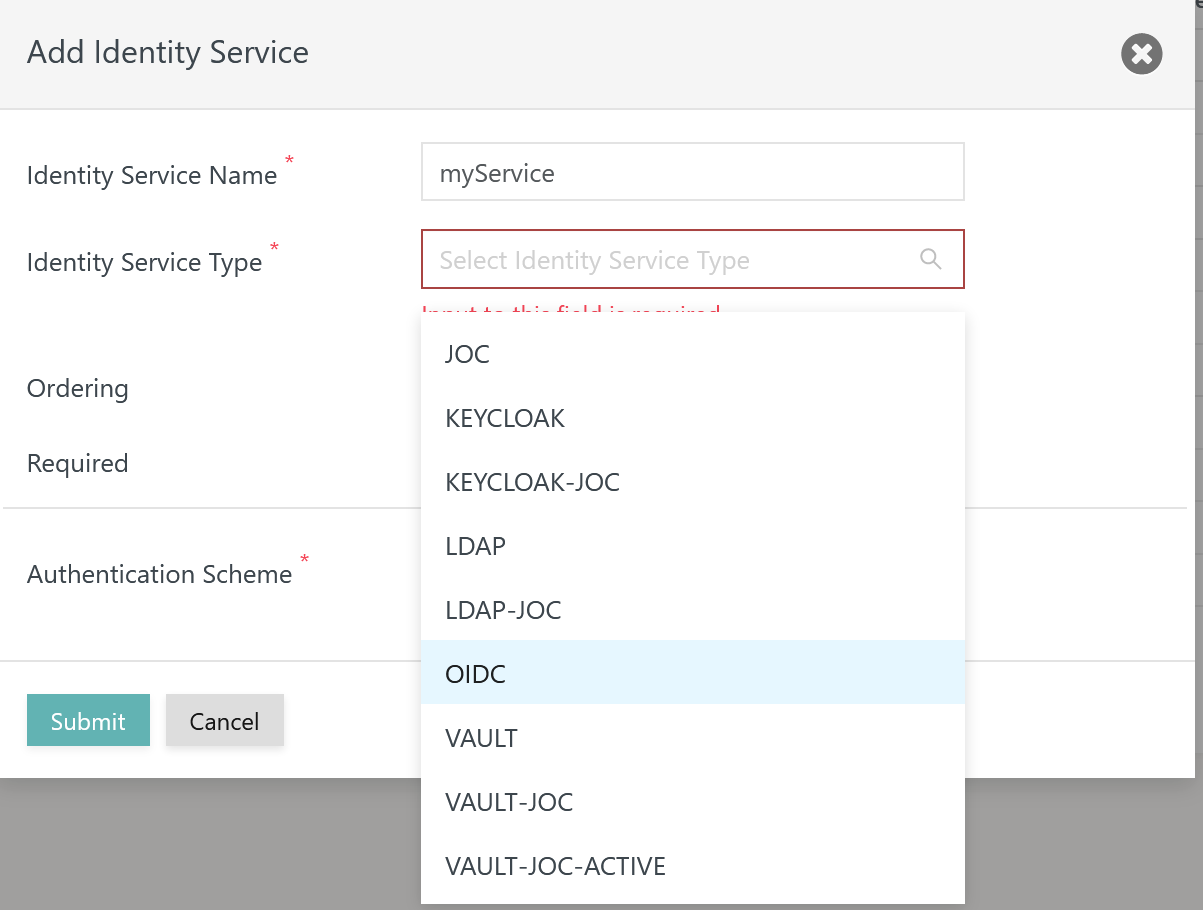
Add Identity Service
To add an Identity Service use the button Add Identity Service from the page shown above, listing the available Identity Services:
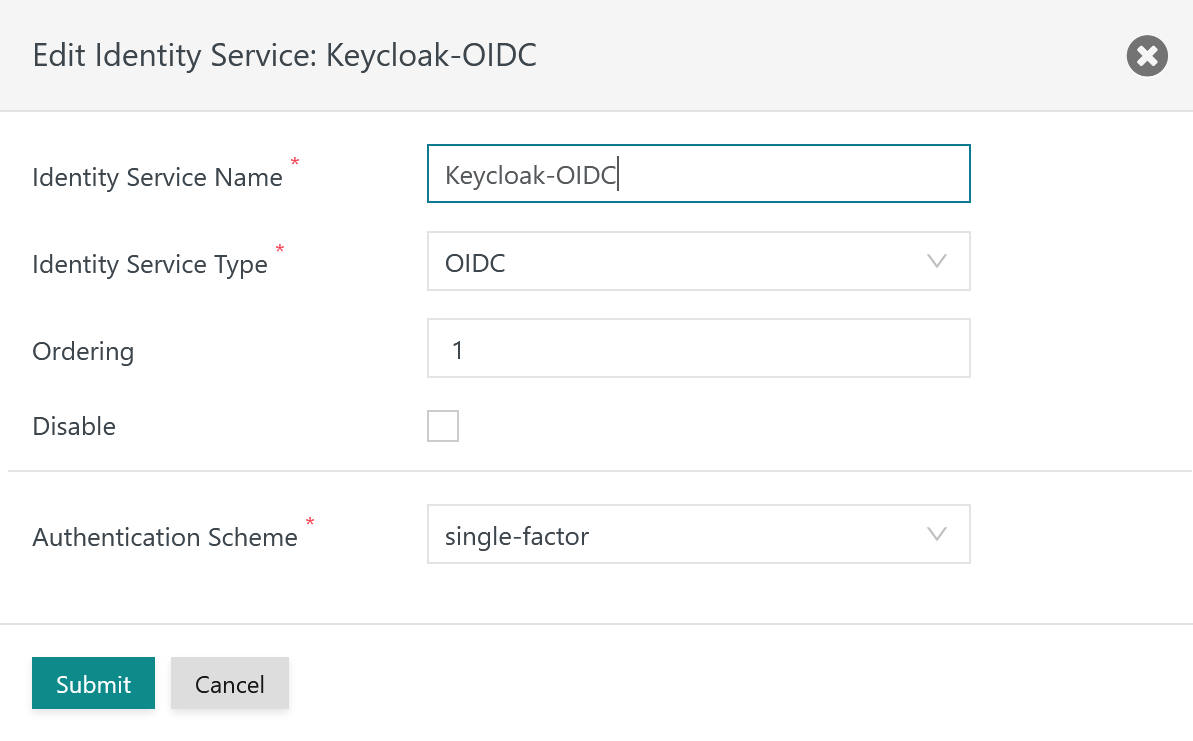
The remaining input fields for the popup window look like this:
Explanation:
...
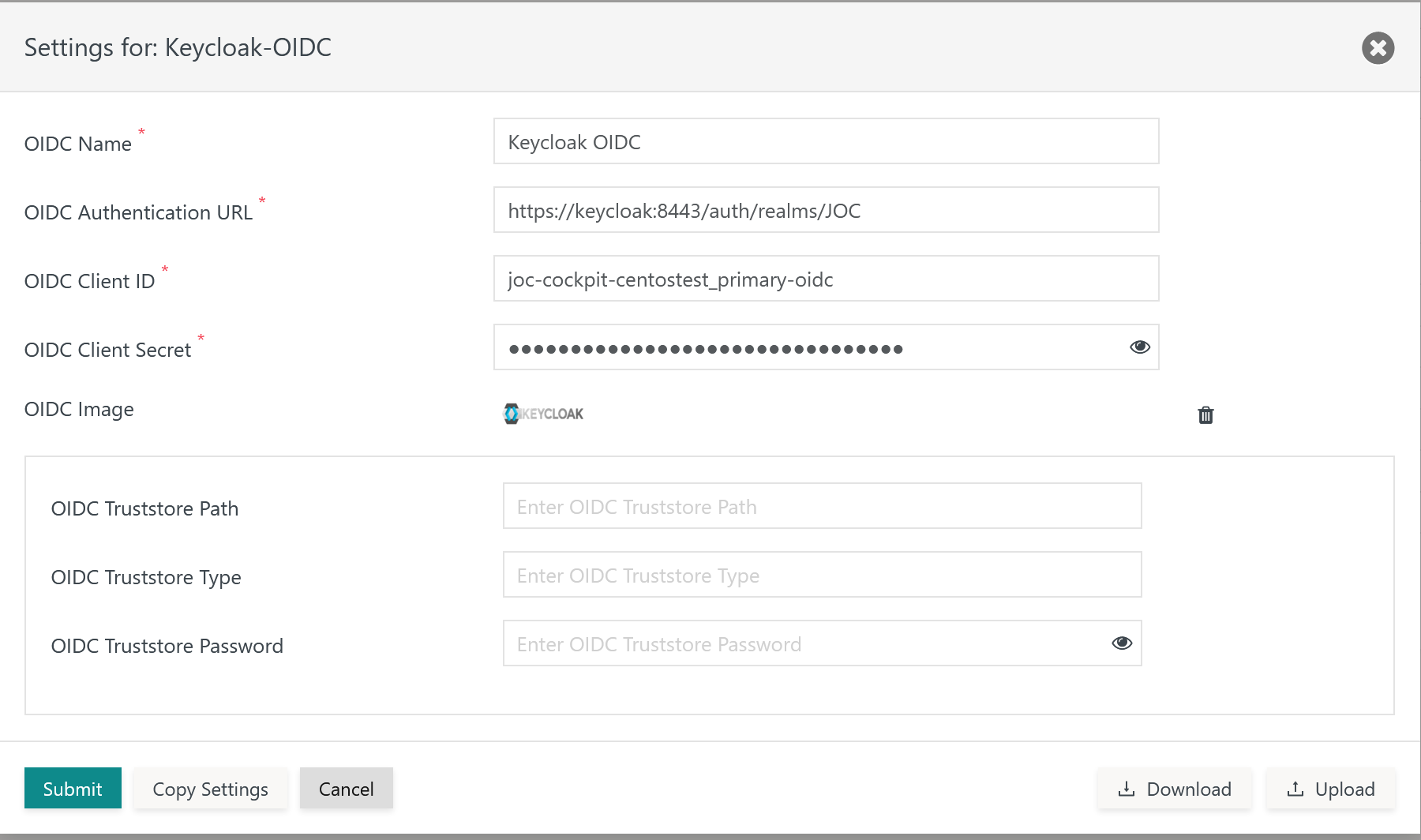
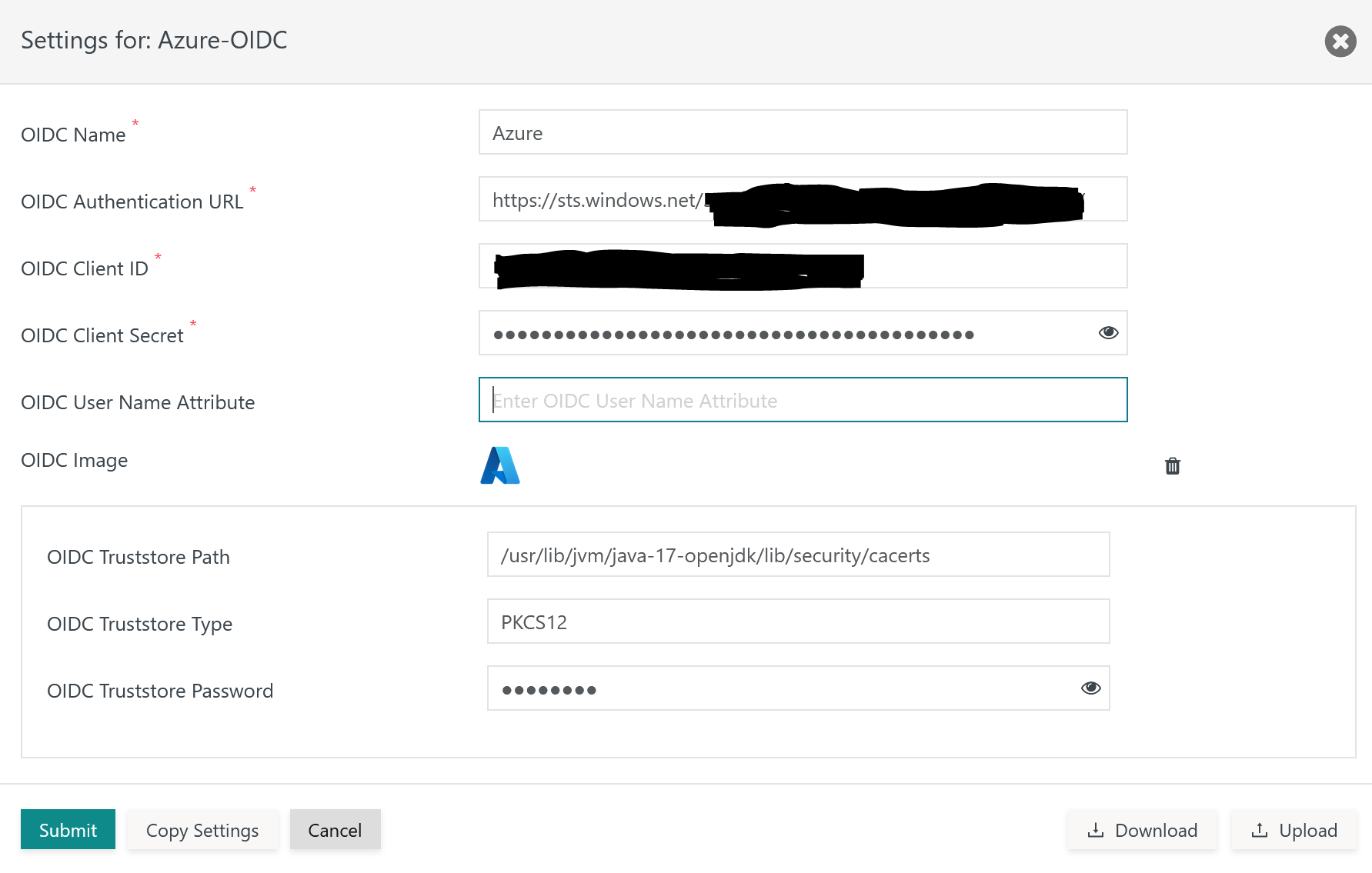
Having added an OIDC Identity Service, it is necessary to add settings for the OIDC integration from the Identity Service's Manage Settings action menu item:
For use with the OIDC Identity Service Type:
- the OIDC Identity Provider product has to be accessible for JOC Cockpit and
- a number of settings have to be specified
Example for Keycloak
Example for Azure
Explanations:
| Name | Value | Description | Example |
OIDC Name | The name of the OIDC Identity Service. | The name of the Identity Service is used by JOC Cockpit to show the caption of the assigned login button. | Google, Keycloak |
OIDC Authentication URL | The URL used by the Client to login to the OIDC Identity Provider. | This URL is called by the Client for login and returns the Access Token from the OIDC Identity Provider. It is similarly used when reading settings of the OIDC Identity Provider with the /.well-known/openid-configuration URL and is used as the issuer during token verification. | Keycloak: https://keycloak:8283/auth/realms/JOC Azure: https://sts.windows.net/<tenant-id>/.well-known/openid-configuration |
OIDC Client ID | The Client ID is configured in the OIDC Identity Provider. | The Client ID is used for a number of calls to to the OIDC Identity Provider. |
|
| The Client Secret is configured in the OIDC Identity Provider. | The Client Secret is used for a number of calls to the OIDC Identity Provider. |
|
OIDC User Name Attribute | The attribute is configured with the OIDC Identity Service. | The attribute is returned by the OIDC Identity Service and identifies the user account.
|
|
OIDC Image | An image can be uploaded that is displayed with the login page. | Optionally an image can be uploaded. . | |
OIDC Truststore Path | The Path to a truststore. | A truststore can be indicated and has to include an X.509 certificate specified for the Extended Key Usage of Server Authentication for the Identity Provider.
| Use of Java truststore: /usr/lib/jvm/java-17-openjdk/lib/security/cacerts |
OIDC Truststore Password | Truststore password | If the indicated truststore is protected by a password then the password has to be specified. | Use of Java truststore: changeit |
OIDC Truststore Type | Truststore type | The type of the truststore is either | Use of Java truststore: PKCS12 |
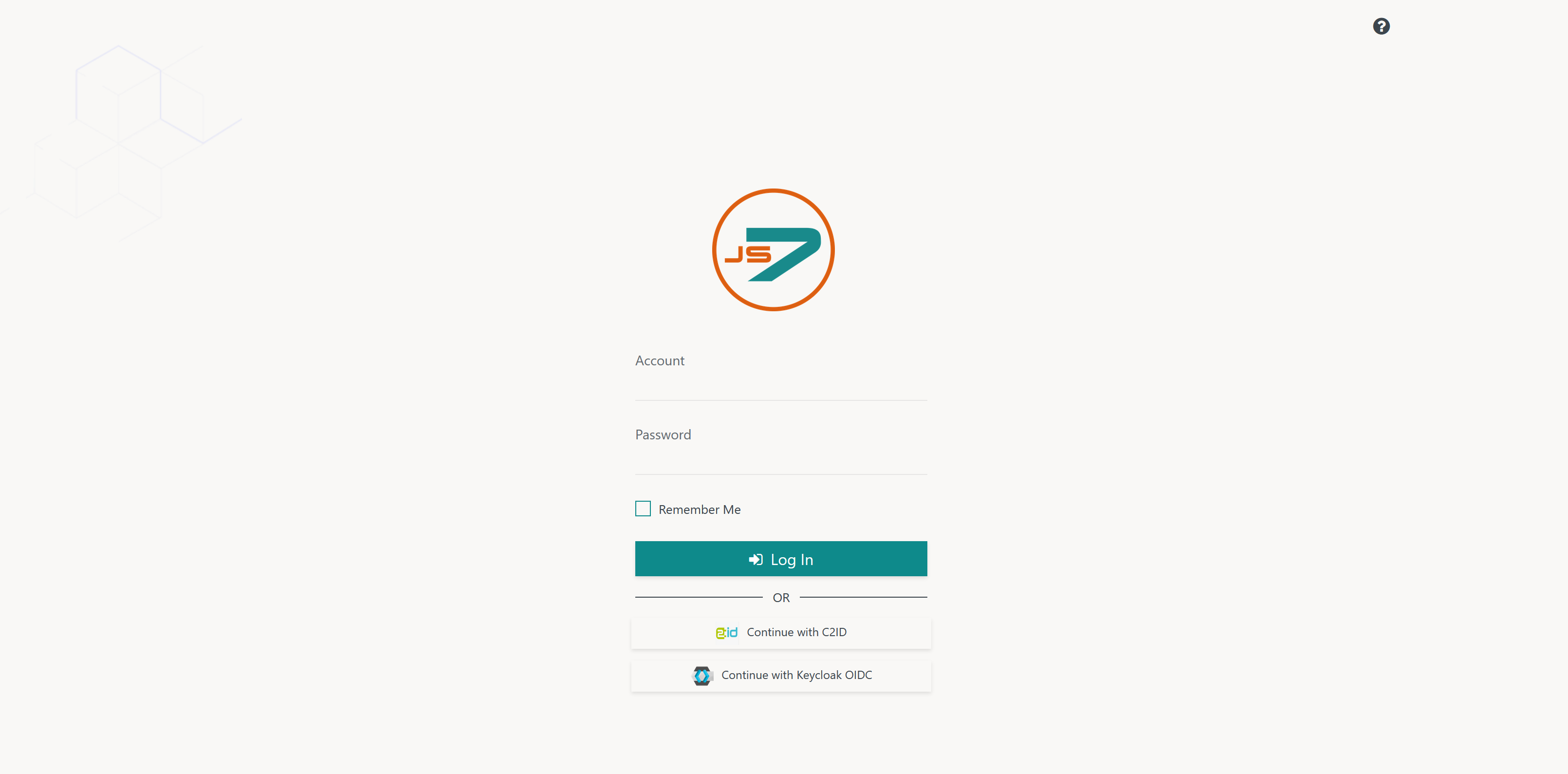
OIDC Login
Once OIDC Identity Services have been configured they are displayed in JOC Cockpit's login screen like this:
Explanation:
...
- client-id: The Client ID which is configured in the JOC Cockpit Identity Service.
- client-secret: The Client Secret which is configured in the JOC Cockpit Identity Service.
- redirect-urls: The list of allowed URLs for redirection after authentication by the Client. Note that the URL of each JOC Cockpit instance has to be specified for clustered JOC Cockpit instances. For JOC Cockpit, the protocol (HTTP, HTTPS), host and port is specified as the URL, for example
https://joc-2-0-primary:4446.
Registration of the Client is performed once in the lifetime of an OIDC Identity Service.
...