Page History
...
- The JS7 - Identity Services offer integration with Keycloak® authentication server Authentication Server.
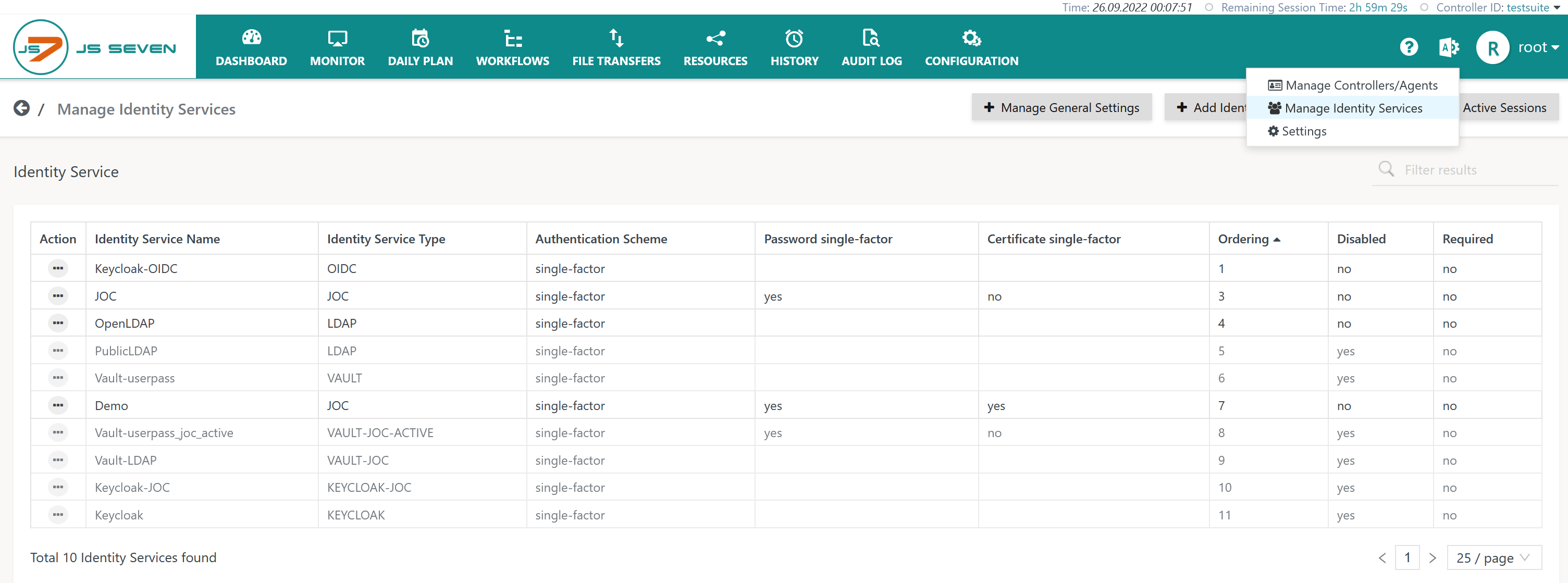
- The Keycloak Keycloak® Identity Service integration is available from JOC Cockpit:
- This requires Keycloak® to be installed and operated by the user. Keycloak® is not a built-in Identity Service Provider and does not ship with JS7.
- JS7 implements a REST client for use with Keycloak® 16.0 and newer.
...
- Service Type:
KEYCLOAK- Management of user accounts and passwords is performed by the Keycloak Server.
- In addition, an automated mapping of roles - assigned a user account in Keycloak - to roles in JOC Cockpit roles takes place.
- The JOC Cockpit does not know any user accounts, passwords and role assignments as this information is managed with Keycloak onlyexclusively.
- Service Type:
KEYCLOAK-JOC- Management of user accounts and passwords is performed by the Keycloak Server.
- The assignment of roles to user accounts is performed with the JOC Cockpit and is stored with the JS7 database.
- The JOC Cockpit knows user accounts and role assignments. The JOC Cockpit does not know passwords as this information is managed with Keycloak onlyexclusively.
Keycloak Authentication Methods
...
- Account & Password
- LDAP
- It is not required to use Keycloak to connect to an LDAP Directory Service as there is a built-in JS7 - LDAP Identity Service for this purpose.
- This authentication method can be used with the
KEYCLOAKIdentity Service Type only.
JS7 does not support cloud based authentication methods with Keycloak.
...
The following objects have to be in place with Keycloak to enable authentication from JOC Cockpit:
- Realm configuration Configuration
- Client configurationConfiguration
- User Accounts
- Roles.
- Roles are used with the Identity Service Type
KEYCLOAK. Roles in Keycloak are not required applicable when using the Identity Service TypeKEYCLOAK-JOC.
- Roles are used with the Identity Service Type
...
It is recommended to create a new realm Realm and not to use the initial master realmMaster Realm.
If no Keycloak Realm is present then it can be added in Keycloak. The default settings are sufficient. The realm must Realm has to be enabled.
Client
If no Keycloak Client is present then it can be added in Keycloak.
- Enabled: On
- Direct Access Grants Enabled: On
- Client Protocol: openid-connect
- Access Type: confidental
- Credentials/Client AutenticatorAuthenticator: Client Id ID and Secret.
- Roles: New Roles roles can be added to the clientClient.
Roles
A admin role must An administrative role has to be added to the realmRealm. The admin role must have at least the client-rolesadministrative role is assigned the following Client Roles:
- realm-management.view-clients
- realm-management.view-users
When If the KEYCLOAK Identity Service Type is used then the names of roles in Keycloak have to match the roles in JOC Cockpit.
When If the KEYCLOAK-JOC Identity Service Type is used then roles in Keycloak are not considered. Instead roles are assigned to accounts in JOC Cockpit..
User Accounts
...
Administrative account
- The admin user must have Keycloak administrative user account has to use password credentials.
- The admin role must be assigned to the admin userKeycloak administrative user account is assigned the "admin" role.
JOC Accounts
For each account that should be able to login into JOC Cockpit, a user must account has to be added.
- Enabled: On
- Required User Actions: none
- Email Verified: Off
- Credentials: Password
- Credentials . Temporary: Off
| Anchor | ||||
|---|---|---|---|---|
|
Account & Password
- The authentication method is available from Keycloak.
- If the
KEYCLOAKIdentity Service Type is used then:- user accounts are managed exclusively by Keycloak,
- roles have to be set up in Keycloak with names that exactly match the names of roles in the JOC Cockpit.
- a user account will be assigned the JOC Cockpit roles matching policy Keycloak role names when performing a login to the JOC Cockpit.
- it is not required to add specific permissions to roles with Keycloak.
- If the
KEYCLOAK-JOCIdentity Service Type is used then:- user accounts are managed by Keycloak.
- user accounts are added to the JOC Cockpit to allow assignment of roles:
- user accounts in Keycloak and in the JOC Cockpit have to match as otherwise the user account is not assigned a role.
- no passwords are managed by the JOC CockpitKeycloak exclusively.
LDAP
- It is not necessary required to use Keycloak to connect to an LDAP Directory Service as there is the built-in in JS7 - LDAP Identity Service for this purpose.
- The authentication method has to be added to Keycloak.
- Authentication with the LDAP authentication service in Keycloak is possible using the
user federation providerLDAP in Keycloak The path of the Authentication Method has to be added to the Identity Service configuration in JOC CockpitKeycloak.
- Authentication with the LDAP authentication service in Keycloak is possible using the
- The
KEYCLOAKIdentity Service Type has to be used, meaning that:- user accounts are managed with Keycloak.
- user accounts are added to the JOC Cockpit to allow assignment of roles:
- user accounts in Keycloak and in the JOC Cockpit have to match as otherwise the user account is not assigned a role.
- no passwords are managed by the JOC CockpitKeycloak exclusively.
Access Tokens
When a user logs in to the JOC Cockpit then user credentials are forwarded to the Keycloak Server that authenticates the user and returns an access token.
- Realms/Tokens
- Client Session Idle: After this idle time a Access Token Lifespan: When exceeding the lifespan an access token will expire. 20s before reaching this time the token will be The access token is automatically renewed by JOC Cockpit 20s before expiration. If Client Session Idle is shorter than Access Token Lifespan then theaccess token will be renewed 20s before Client Session Idle expires.
- Client Session Idle: After the idle timeout the session will expire. The access token and implicitly the session are automatically renewed by JOC Cockpit automatically20s before idle timeout.
- Client Session Max: After this time period a token session can no longer be renewdrenewed. It is recommended to set this value to a larger value then the session timeout configured in JOC Cockpit.
- SSO Session Idle: When Used when Client Session Idle is not set.
- SSO Session Max: When Used when Client Session Max is not set.
- Keycloak access tokens are created with the following restrictions:
- time Time to live Live (TTL):
- the The access token will expire after the given period (Access Token Lifespan).
- The session will expire after the given period (Client Session Idle)
- the The Identity Service renews the access token 20s before expiration of the session or of the access token, this step is performed until Session Max is reached. This requires that the access token's TTL exceeds 60s and that the Keycloak permission for renewing a renewal of an access token by the token its owner to be is in place.
- maximum time Maximum Time to liveLive:
- the The access token's overall lifetime is limited (Session Max), renewals cannot take place after the specified period.
- time Time to live Live (TTL):
- If an access token cannot be renewed by the Identity Service then the user session is terminated and the user is forced to login and to specify credentials.
- This happens in the event of that the maximum TTL being is exceeded or that the token has been is revoked.
- Keycloak administrators should check for reasonable values of the session TTL (Session Idle) and the Access Token Lifespan, maybe not less than 300s, and the maximum TTL (Session Max) , maybe typically at least 15 minutes, as otherwise users would will have to repeatedly login quite frequently.
- The JOC Cockpit handles the idle timeout of user sessions independently of from Keycloak, see JS7 - Identity Services.
- If the idle timeout is exceeded then the user session is terminated.
- The Identity Service can will revoke the access token with the Keycloak serverServer on termination of the user session.
Identity Service Configuration
The The icon in the JOC Cockpit Manage Identity Services page from the user menu of an administrative account is provided for the configuration of Identity Servicesmain menu is used to select the Manage Identity Services page:
Add Identity Service
To add an Identity Service use the button Add Identity Service from the page shown above, listing the available Identity Services:
...
- The
Identity Service Nameis a unique identifier that can be freely chosen. - The
Identity Service Typecan can be selected as available from the above matrixlist. - The
Orderingspecifies the sequence in which a login is performed with available Identity Services. - The
Requiredattribute specifies if login with the respective Identity Service is required to be successful, for example if a number of Identity Services are triggered on login of a user account. - The
Identity Service Authentication Schemeallows to selectsingle-factorauthentication: user account and password are specified for login with the Identity Service.two-factorauthentication: in addition to user account and password a Client Authentication Certificate is required - see the JS7 - Certificate based Authentication article for more information.
...
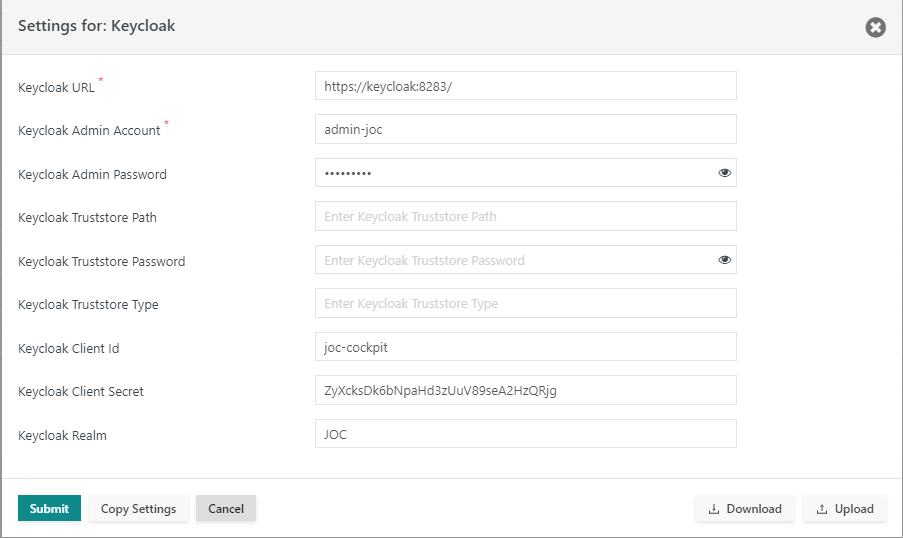
Having added a Keycloak Identity Service it is necessary required to add settings for the Keycloak integration from the Identity Service's Manage Settings action menu item:
For use of with the Keycloak Identity Service:
- the Keycloak product has to be installed and has to be accessible for JOC Cockpit and
- the following settings have to be specified:
Explanation:
Keycloak URL: the base URL for which the Keycloak REST API is available.Keycloak Administration Account: A Keycloak Account account with the admin an administrative role that have at least the roles realmis assigned the realm-management.view-clients and realm and realm-management.view-users roles.- This The administration account is used to retrieve the roles for a Keycloak account and for renewing access tokens.
Keycloak Administration Password: The password for theKeycloak Administration Account.Keycloak Truststore Path: Should the Keycloak Server be configured for HTTPS connections then the indicated truststore has to include an X.509 certificate specified for the Extended Key Usage of Server Authentication.- The truststore can include a self-signed certificate or a CA signed certificate. Typically the Root CA certificate is used as otherwise the complete certificate chain involved in signing the Server Authentication Certificate has to be available with the truststore.
- If the Keycloak Server is operated for HTTPS connections and this setting is not specified then the JOC Cockpit will use the truststore that is configured with the
JETTY_BASE/resources/joc/joc.propertiesconfiguration file. This includes use of settings for the truststore password and truststore type. - The path to the truststore is specified relative to the
JETTY_BASE/resources/jocdirectory. If the truststore is located in this directory then only the file name is specified, typically with a .p12 extension. Other relative locations can be specified using, for example,../../joc-truststore.p12if the truststore is located in theJETTY_BASEdirectory. An absolute path cannot be specified and a path cannot be specified that lies before theJETTY_BASEdirectory in the file system hierarchy.
Keycloak Truststore Password: If the Keycloak Server is configured for HTTPS connections and the indicated truststore is protected by a password then the password has to be specified.Keycloak Truststore Type: If the Keycloak Server is configured for HTTPS connections then the type of the truststore has to be specified being eitherPKCS12orJKS(deprecated).- Keycloak Clients are entities that request Keycloak to authenticate a user account. For example, an application such as JOC Cockpit or service acts as a Client to the Keycloak serverServer. Clients use Keycloak to authenticate and to provide a single sign-on solution.
Keycloak Client IDandKeycloak Client Secretare used for- requesting a valid an access token
- for user authentication,
- for admin administrative access,
- validating an existing access token,
- renewing an existing valid access token.
- requesting a valid an access token
Keycloak Client Secret:The Client has owns a secret which needs to be known by both the Keycloak server Server and the JOC Cockpit.
Keycloak Realm: A realm manages a set of users, credentials, roles, and groups. A user belongs to a realm and performs a login to a realm. Realms are isolated from each other and , they manage and authenticate exclusively user accounts that they control.
...