...
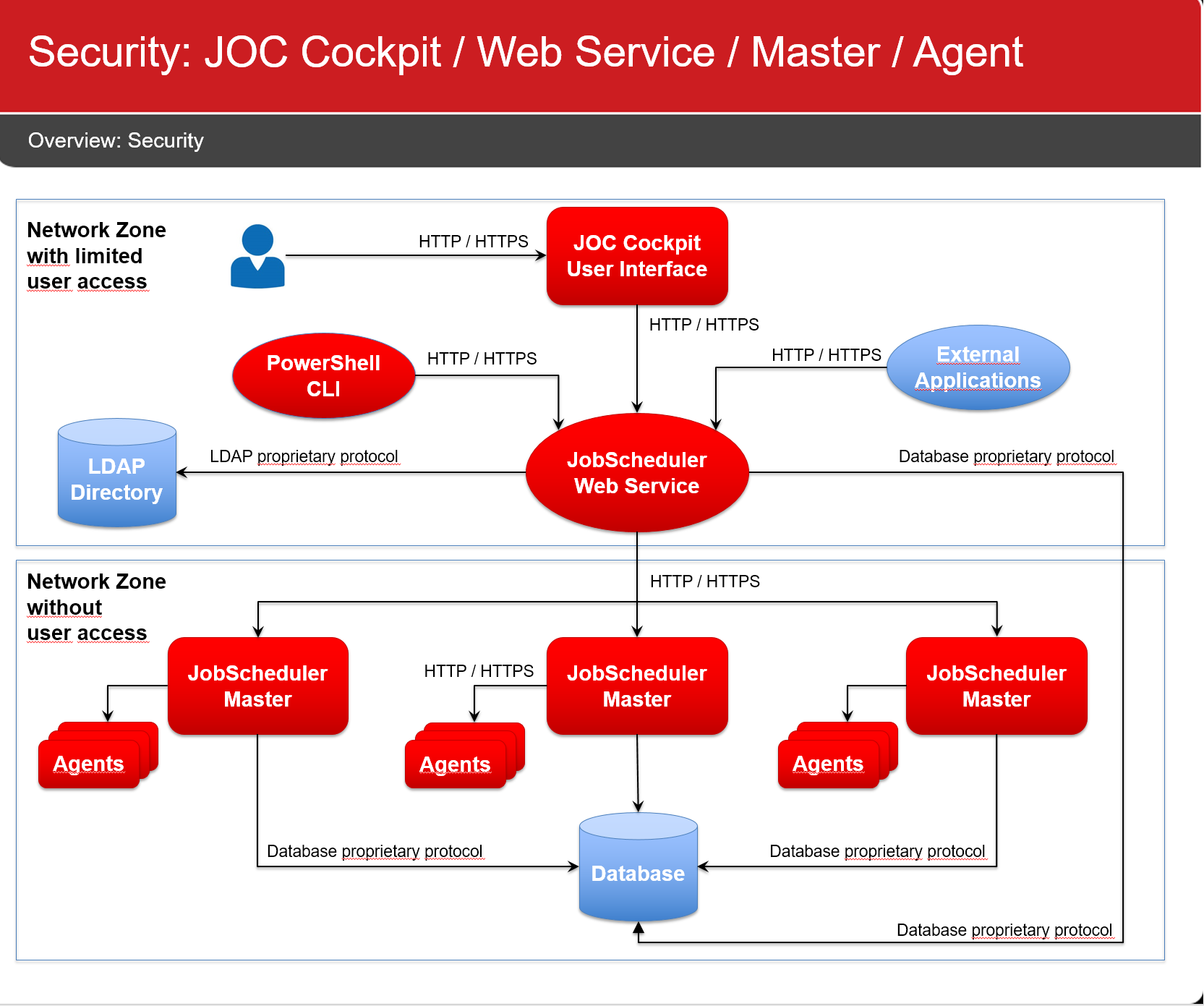
JobScheduler components use the following connections:
Network Connections
All network connections are unidirectional, as indicated by the direction of the arrows in the above diagram.
...
- All network connections make use of HTTP
- Connections from a user browser to the JOC Cockpit
- Connections from the PowerShell CLI to the JOC Cockpit REST Web Service
- Connections from the JOC Cockpit REST Web Service to the JobScheduler Master
- Connections from the JobScheduler Master to Agents
- Port Usage
- The JOC Cockpit can be accessed at port 4446
- The JOC Cockpit REST Web Service can be accessed at port 4446
- The JobScheduler Master uses the following ports:
- Access to the JobScheduler Master Web Service at port 40444
- Access to the JobScheduler Master via TCP at port 44444444
Display feature availability EndingWithRelease 1.12 - Access to the JobScheduler Master via UDP at port 44444444
Display feature availability EndingWithRelease 1.12 - The TCP port 4444 and HTTP port 40444 enable access to the "classic" JOC GUI.
Jira server SOS JIRA columns key,summary,type,created,updated,due,assignee,reporter,priority,status,resolution serverId 6dc67751-9d67-34cd-985b-194a8cdc9602 key JOC-304
- The JobScheduler Agent listens to port 4445
- Network Interface Usage
- By default JobScheduler components will listen to the above mentioned ports on all available network interfaces.
- Firewall Settings
- Open ports in your firewall exclusively for the hosts, protocols and ports as specified above. Consider allowing connections only for the directions indicated in the diagram above.
...
- Configure network connections to use HTTPS
- The use of HTTPS includes users providing valid certificates for the hosts that JobScheduler components are operated for. The use of self-signed certificates is a no-go.
- As HTTPS is restricted to secure the connection, in addition authentication is added to the configuration, e.g. when using HTTPS then a JobScheduler Master is configured to authenticate with an Agent in order to guarantee that the Master is what it claims to be and is entitled to access an Agent.
- For detailed instructions on the configuration see:
- JOC Cockpit - HTTPS Authentication explains HTTPS configuration for the JOC Cockpit and connection to the JobScheduler Master.
- JobScheduler Universal Agent - HTTPS Agent and Master Authentication
- Drop the JobScheduler Master TCP / UDP port:
- This port is not required for standard operation with releases starting from 1.11.
- This port is required for previous releases that include the "classic" JOC GUI running in the JobScheduler Master.
- Access to this port can be restricted with the
<allowed_host>setting in./config/scheduler.xml
- Access to this port can be restricted with the
- This port is required for all releases if a JobScheduler Supervisor is used.
- Restrict use of network interfaces
- Consider restricting JobScheduler components to only listen to specific network interfaces.
- The JobScheduler Master can be configured by use of the
http_portandhttps_portattributes in the./config/scheduler.xmlconfiguration file. - Configure the JobScheduler Universal Agent to use the
SCHEDULER_HTTP_PORTandSCHEDULER_HTTPS_PORTenvironment variables in the JobScheduler Agent instance script.
- Drop the "classic" JOC GUI
- The "classic" JOC GUI ships without authentication and authorization. It is included with release 1.11 for users who stick to this interface. It is available from the above TCP port and HTTP port.
Display feature availability EndingWithRelease 1.12 - To drop the "classic" JOC GUI remove the
SCHEDULER_HOME/operations_guifolder.
- The "classic" JOC GUI ships without authentication and authorization. It is included with release 1.11 for users who stick to this interface. It is available from the above TCP port and HTTP port.
...
- Consider the hints from the JOC Cockpit - Security article
- The JOC Cockpit REST Web Service ships with a default configuration in
./joc/resources/joc/shiro.inithat includes- using local authentication with accounts and passwords stored in clear text.
Display feature availability EndingWithRelease 1.11.4 - using local authentication with accounts and passwords stored as hash values.
Display feature availability StartingFromRelease 1.11.5 - using local role assignment
- the following default values for accounts, passwords and assigned roles (see JOC Cockpit - Authentication and Authorization for more informatio):
administrator=secret, administratorapplication_manager=secret, application_managerit_operator=secret, it_operatorincident_manager=secret, incident_managerbusiness_user=secret, business_userapi_user=secret, api_userroot=root, all
- using local authentication with accounts and passwords stored in clear text.
- The JobScheduler Master is assumed not to be accessed by users directly but exclusively via the JOC Cockpit REST Web Service. No default authentication is provided.
- JobScheduler Universal Agents are assumed not to be accessed by users directly but exclusively by a JobScheduler Master. No default authentication is provided.
...
- Do not use the default configuration with local authentication for the JOC Cockpit REST Web Service.
- Instead use LDAP authentication as explained in with the JOC Cockpit - Authentication and Authorization section.
- Do not allow any network connections to the JobScheduler Master and Agents except as stated above. This makes any authentication mechanism unnecessary.
Credentials Management
Database Credentials
...
- It is a bad idea to run a JobScheduler Master or Agent using a Unix root account or Windows Administrator account.
- Certainly this makes life easy when it comes to switching to other user accounts or accessing files.
- However, you should not grant more permissions to a process than required.
- Use specific user accounts to run JobScheduler Masters and Agents:
- Do not use the system account (Windows) or root (Unix).
- Create specific service accounts that are limited to privileges that are required to execute jobs.
- Do not specify credentials for Windows Service accounts during installation:
- The installer will store such credentials in its installation response file (Master:
jobscheduler_install.xml, Agent:jobscheduler_agent_install.xml) - Instead, use the Windows Service Panel to manually specify credentials for the service account.
- The installer will store such credentials in its installation response file (Master:
- There are a number of options when it comes to running jobs for different user accounts:
- For Unix environments
- Your job scripts can switch to a different user context by use of
sudoorsucommands.sudois the preferred option as this the standard Unix tool that allows secure configuration of the users that are allowed to execute certain commands (sudoers file). In additionsudoprovides reporting capabilities about (ab)use of commands.
- Your job scripts can switch to a different user context by use of
- For Windows environments
- You can use the Windows Credential Manager to safely store credentials of the user account that a job should be executed for. The JobScheduler will then read the credentials and create a new process to run a job in the target user context. This is the preferred solution as it does not store credentials with the JobScheduler configuration.
- Find detailed information from the JobScheduler Universal Agent - Running jobs as a different user article.
- For all environments
- You can run a number of Agents in parallel for different user accounts.
- For details see the JobScheduler Universal Agent - Running multiple instances article.
- For Unix environments
- For jobs that require credentials, e.g. to access a database, a credential store can be used, see the Using a Credential Store for Jobs article.
- Credentials are not provided from parameters (that could be logged in clear text), instead an interface is provided that allows on demand access to the credential store.
- This feature is available for Shell jobs and for API jobs (JavaScript, PowerShell etc.).
File Transfer Credentials
...
- Use the YADE Credential Store to manage credentials centrally in a store that is referenced by YADE configuration items, see the How to set-up the Credential Store and YADE Parameter Reference - CredentialStoreFragment articles.
- Should you use FTP connections then consider to switch to use of SFTP.
- SFTP connections can be used with private/public key files, there is no need to use passwords for such connections.
Further Resources
| Display children header |
|---|