Page History
...
Each user with the permission to deploy has to add its their X.509 signing certificate to JOC Cockpit:
...
In addition, the X.509 certificate of the Root CA that which signed the user's signing certificate can be added to JOC Cockpit. There is a single Root CA certificate for all user profiles.
...
- Any user signing certificates have to be rollout rolled out to the Controller and Agents. Certificates are stored to in the
config/private/trusted-x509-keysfolder of Controller and Agent installations. - If a Root CA certificate is present in JOC Cockpit, then it is sufficient to add the Root CA certificate to the
config/private/trusted-x509-keysfolder of Controller and Agent installations.- No further user
signingcertificates have to be added to the Controller or Agents as long as the user signing certificates is created by the given Root CA. - This mechanism implies that any user signing certificate signed by the same Root CA certificate will be accepted.
- Users who do not wish to use this implicit mechanism should not add the Root CA certificate to the Controller and Agents but should only add individual user signing certificates only.
- No further user
Deployment Process Overview
The user has to export the desired configuration of scheduling objects with the Export operation available from the Configuration view.
- Deployment tasks include to:
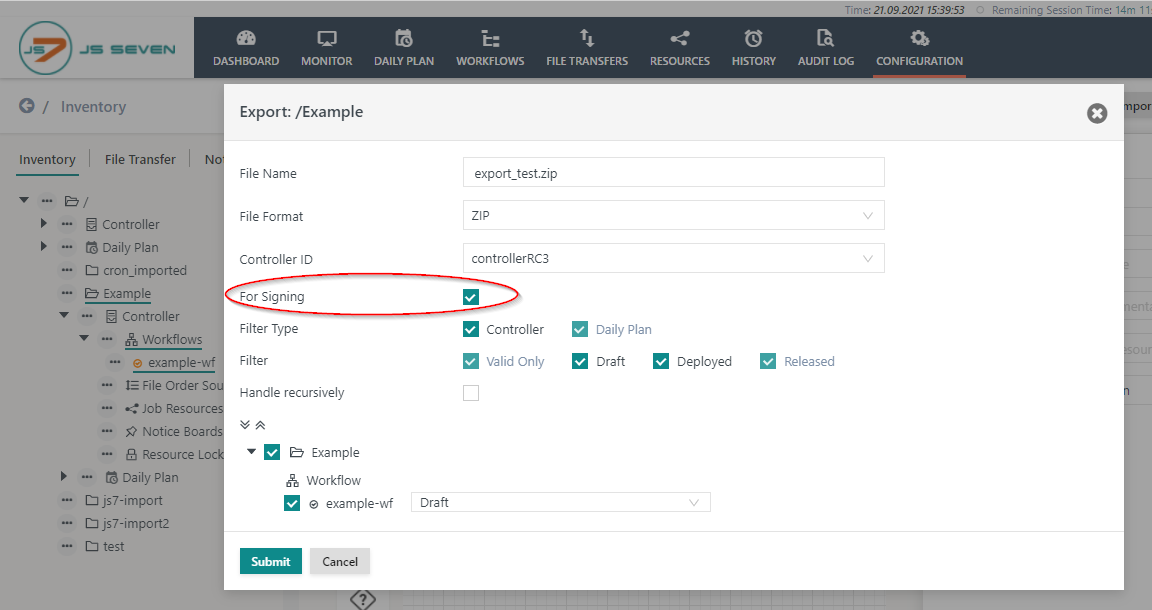
export Exporting scheduling objects with the checkbox "for Signing" checked to an archive file (.zip).
- unpack Unpacking the exported archive.
- The archive contains a
meta_inffile and the configurations.
- The archive contains a
- sign Signing the configuration files of scheduling objects and store storing the signature - base64 encoded - in a file with in the same folder.
- Each Note that each signature file has to use the same name as the original configuration file of the scheduling object with an additional filename extension.
- for RSA/ECDSA signatures use the filename extension ".pem" or ".sig" respectively.
- for PGP signatures use the default filename extension ".asc".
- pack Packing the archive once again to add the signature files and make sure that the
meta_inffile is still available with the root folder of the archive. - upload Uploading the archive using the Import And Deploy button.
...
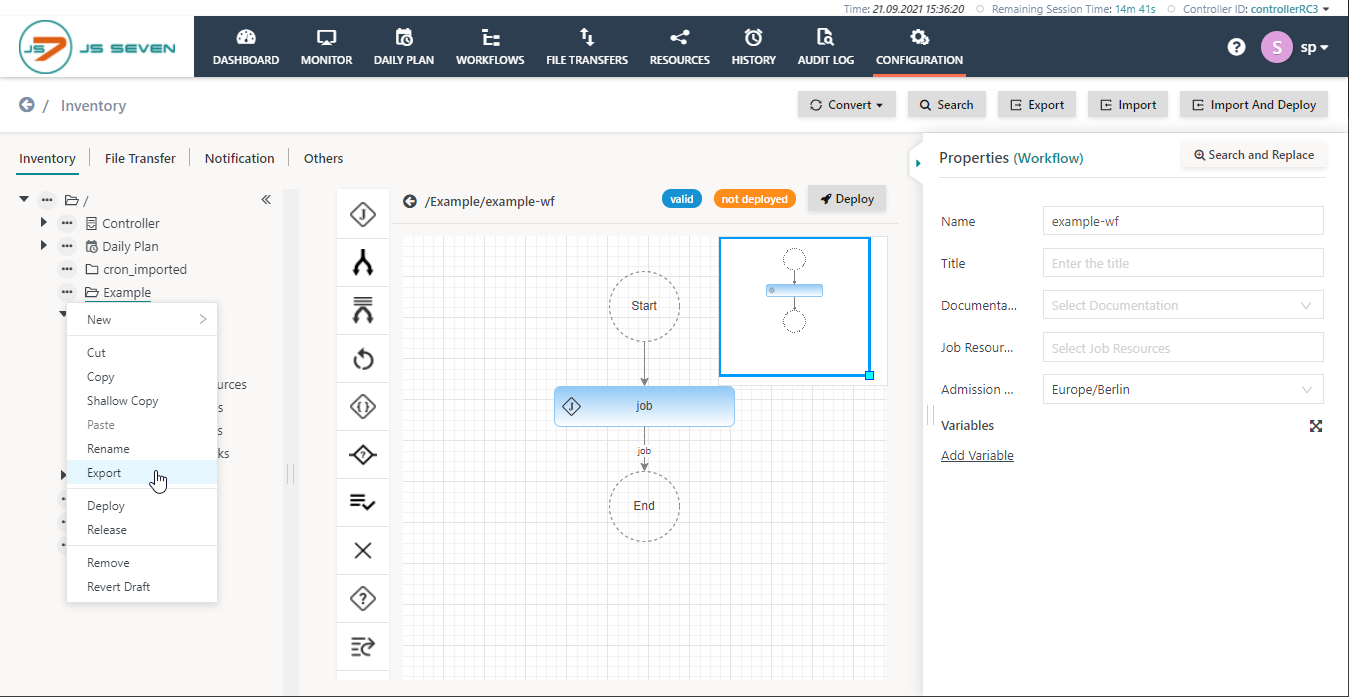
- Click Export in the context menu of the folder to export or from the button in the top right corner:
- In the Export popup window check the checkbox for Signing:
- Select the scheduling objects to deploy.
Signing
It is recommended to perform that the signing procedure is performed on a secure device. It is essential that the signing process is performed in a secure manner outside of the server running the JOC Cockpit.
Extract the configuration from the archive and preserve the folder structure of the included scheduling object files:
...
-sha256- the signer algorithm
-sign c:\tmp\sos.private-ec-key.pem- the private key file to sign the content of the original configuration file
-out c:\tmp\example-wf.workflow.json.sha256- the path to the output file
- the file contains containing the binary representation of the signature
c:\tmp\example-wf.workflow.json- the path to the original scheduling object file (in this example: workflow)
- the path to the original scheduling object file (in this example: workflow)
...
base64- OpenSSL switch to encode base64
-in c:\tmp\example-wf.workflow.json.sha256- the newly created binary signature file
-out c:\tmp\example-wf.workflow.json.pem- the base64 encoded text signature file according to the JOC Cockpit deployment naming convention
The procedure to add for adding scheduling object files and signatures to an archive includes the following steps:
- Copy Copying the newly created text signature files to the same folders as the scheduling object files.
- Pack Packing the archive once again or add adding the signature files to the existing archive.
- The exported archive contains the
meta_inffile. This file does not have to be signed. Make sure the file is present in the root folder of the target archive.
- The exported archive contains the
- ImportImporting/Deploy Deploying this archive with the Import And Deploy function of JOC Cockpit.
...