YADE Credential Store
More information about the Credential Store can be found in the following articles:
- YADE Credential Store
- Using Credential Store to securely store authentication, connection and other parameters
Setting up a Credential Store
Download KeePass and create kdb file
- YADE Credential Store (CS) supports KeePassX DB version 1.0
- One can download the KeePassX desktop utility from https://www.keepassx.org/downloads/
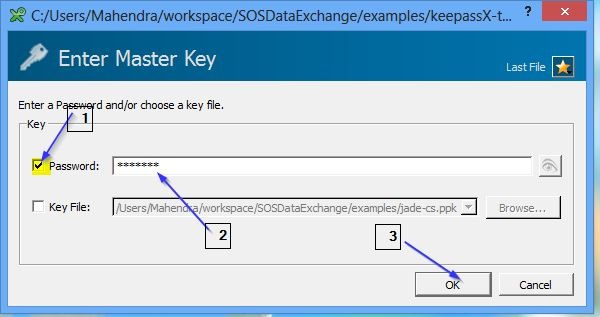
Set-up Credential Store with Password
Step 1: Setup KeePassX DB
- Open the KeePassX utility
- Choose password as Master Key
- Assign password to KeePass DB and click OK
YADE will use the Master Key, i.e. the password specified during the creation process as access password of the KeePassX database.
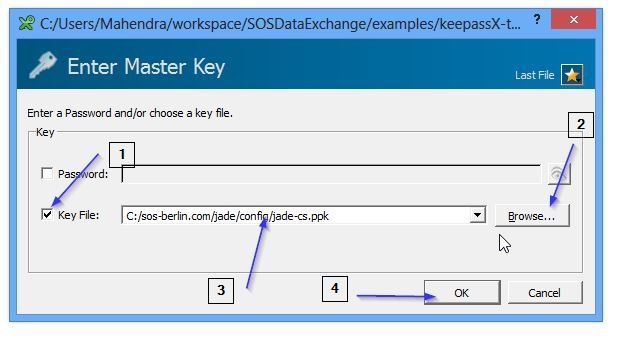
Set-up Credential Store with PPK key
- Start KeePassX utility
- Click on Key File as Master Key
- Browse for pre-generated SSH key as Master Key
- Click ok and KeePassX will open and will be ready to add new entries.
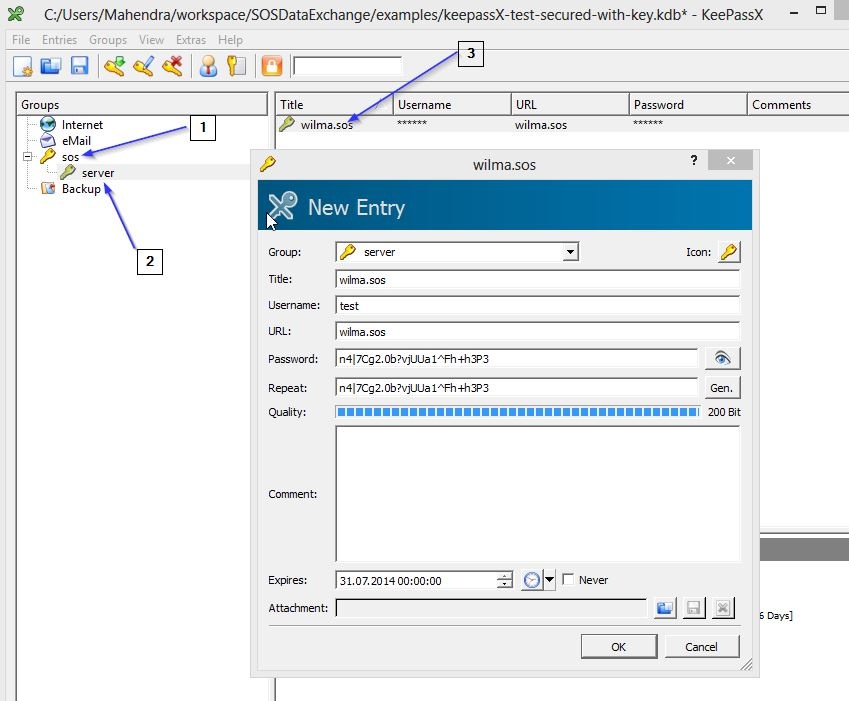
Create Credential Store entries
Create Credential Store entry for FTP server
KeePassX DB can organize entries in logical groups, under groups and sub-groups.
One can organize Credential Store in groups, e.g. Internal-Server, External-Server etc. User is free to choose his own organization scheme.
- Create new top group i.e.
sos - Create new sub group i.e.
server - Create new entry
wilma.sosfor settings- Title : Will be used as key in the hierarchy to access the credentials.
- Username : Field is used to specify the username, i.e. FTP, SFTP user name
- Password : Field is used to specify the password, user can use the KeePassX's password generation feature to specify strong passwords or can provide existing password.
- Comment : Can contain extra parameters for YADE along with credentials, any YADE parameter can be specified in the comment section.
- Expires : Expiry date is used to enforce a password and SSH key expiration policy. The user can define the expirarion period, e.g. 90 days, or check option
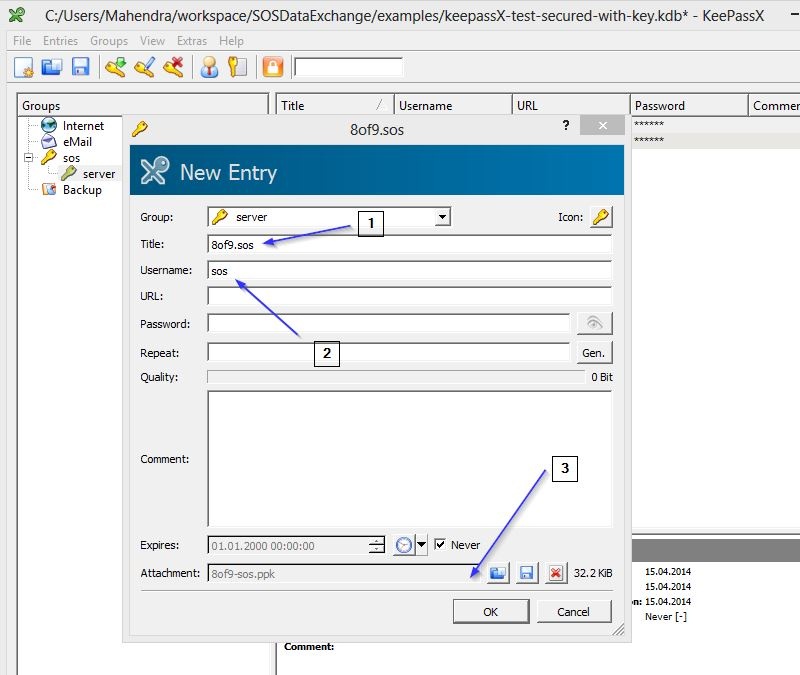
never. YADE will raise an error if a KeePassX DB entry is expired. - Attachment : Can contain private key file used for file transfer
Create Credential Store entry for SFTP server
YADE profiles with Credential Store
Set-up global Credential Store profile
Define a global profile containing all the parameters concerning Credential Store. YADE can reuse any profile defined in same jade_settings.ini file.
It is recommended to create profile fragments and reuse them in profiles.
Alternatively a user can define multiple KeePassX DB files, e.g. Test, Integration, Production, and create corresponding profiles for the different environments.
Set-up global Credential Store profile with password
; Global Profile for KeePassX Database WithPassword [Keepass_DataBase_WithPassword] use_credential_Store = true CredentialStore_FileName = C:\sos-berlin.com\jade\credential-store\keepassX-test.kdb CredentialStoreAuthenticationMethod = password CredentialStore_password = *********
Set-up global Credential Store profile with public key
; Global Profile for KeePassX Database With Public Key [Keepass_DataBase_WithPublicKey] use_credential_Store = true CredentialStore_FileName = C:\sos-berlin.com\jade\credential-store\keepassX-test.kdb CredentialStoreAuthenticationMethod = privatekey CredentialStore_KeyFileName = C:\sos-berlin.com\jade\config\jade_cs_rsa.ppk
Set-up YADE profile for FTP
In this example we are including Credential Store settings from a global KeePassX database profile Keepass_DataBase_WithPassword .
YADE then will open the KeePassX DB and refer to the entry sos/server/wilma.sos that has previously been defined in the KeePassX DB:
source_CredentialStore_KeyPath: YADE will refer to the entry from KeePassX DB.
source_include: include Credential Store settings.
[ReceiveUsingKeePass]
source_include = Keepass_DataBase_WithPassword
source_CredentialStore_KeyPath = sos/server/8of9.sos
source_dir = /tmp/test/jade/out
source_make_dirs = true
source_transfer_mode = ascii
target_protocol = local
target_dir = ${TEMP}/jade/in
operation = copy
file_spec = \.txt$
transfer_mode = ascii
Set-up YADE profile for SFTP
[ReceiveUsingKeePassSourceSFTP]
operation = copy
file_spec = \.txt$
;;
source_include = Keepass_DataBase_WithPassword
source_CredentialStore_KeyPath = sos/server/8of9.sftp.sos
source_dir = /tmp/test/jade/out
source_protocol = SFTP
source_ssh_auth_method = password
;;
target_protocol = local
target_dir = ${TEMP}/jade/in
Example for Server-to-Server File Transfer profile using Credential Store
A profile definition for Server-to-Server File Transfer, from an FTP to na SFTP server:
[transfer_server_2_server]
include = Keepass_DataBase_WithPassword
file_spec = ^.*\.txt$
operation = copy
source_CredentialStore_KeyPath = sos/server/wilma.sos
source_dir = /tmp/test/jade/out
target_CredentialStore_KeyPath = sos/server/8of9.sos
target_dir = ${TEMP}/jade/in
In this example all files with the file name extension .txt should be transferred from the server wilma via FTP to the server 8of9 by SFTP.
To start this from the command line you would type:
jade.sh -settings=name_of_settings_file -profile=transfer_server_2_server
Profile fragments SFTP with Public Key
To make the profile reusable and more readable it is possible to reuse profiles snippets in the way like this:
TODO
[ReceiveUsingKeePass]
source_include = Keepass_DataBase_WithPassword
source_source_CredentialStore_KeyPath = keepass_homer_sftp_key
source_dir = /tmp/test/jade/out
source_protocol = sftp
source_CredentialStore_ExportAttachment = true
source_CredentialStore_ExportAttachment2FileName = c:\temp\8of9-sos.ppk
source_ssh_auth_method = publickey
source_ssh_auth_file = c:\temp\8of9-sos.ppk
source_make_Dirs = true
source_transfer_mode = ascii
target_protocol = local
target_dir = ${TEMP}/jade/in
operation = copy
file_spec = \.txt$
transfer_mode = ascii
Profile fragments SFTP with Public Key
To make the profile reusable and more readable it is possible to reuse profiles snippets in the way like this:
TODO
See also
- Using Credential Store to securely store authentication, connection and other parameters]
- For information about the YADE parameters see the YADE - Reference Documentation - Parameter Reference