LDAP Configuration items
We refere in this document to a public LDAP server. To configure a realm for accessing the public LDAP server please add
publicLdapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
publicLdapRealm.userDnTemplate = uid={0},dc=example,dc=com
publicLdapRealm.searchBase = dc=example,dc=com
publicLdapRealm.contextFactory.url = ldap://ldap.forumsys.com:389
publicLdapRealm.groupNameAttribute = ou
publicLdapRealm.userNameAttribute = uid
publicLdapRealm.userSearchFilter = (uniqueMember=uid=%s,dc=example,dc=com)
publicLdapRealm.groupRolesMap = \
scientists : it_operator, \
mathematics: all
There are some configuration items that configure the ldap realm that should be used. These items can not be changed with the Account Management in JOC.
| Key | Value | Description |
|---|
| ldapReam | com.sos.auth.shiro.SOSLdapAuthorizingRealm | The key is the name of the realm. You can define any name. The name is taken as a reference to set the properties of the realm. The value is the name of the class that implements the realm. The implementation from SOS extends org.apache.shiro.realm.ldap.JndiLdapRealm |
ldapRealm.contextFactory.url | ldap://host:port | The host and the port of your LDAP server. You can check whether the server is reachable with telnet host port Make sure that the firewall is open for the given port. |
ldapRealm.useStartTls | true|false | To enable starttls set the value to true (Default is false) Please note the the server must be prepared to serve with Starttls. To check this, you can use a LDAP browser like "Softerra LDAP Browser". Configure your LDAP Server there and click the "Enable Starttls Button" On Client Site you will need the certificate and you have to add the certificate to your truststore. The path of your truststore is definied in the JOC configuration file joc.properties. truststore_path = path to your truststore.
e.g. C:/Program Files/Java/jdk1.8.0_131/jre/lib/security/cacerts or ../../etc/joc.jks
|
ldapRealm.hostNameVerification | on|off true|false | To enable the host name verification of the certificate. The default is off. |
rolePermissionResolver | com.sos.auth.shiro.SOSPermissionResolverAdapter | The implementation of the permission resolver. The SOS implementation sets an org.apache.shiro.realm.text.IniRealm to resolve the permissions. That means that the permissions a role have are specified in the configuration file shiro.ini in the same way it is done when using the iniRealm. |
ldapRealm.rolePermissionResolver | $rolePermissionResolver | Sets the role permission resolver for the ldap realm. |
securityManager.realms | $ldapRealm | Sets the list of realm that should be used for authentication. This is a comma seperated list of realms. e.g. $ldapRealm --> Only one realm specified $ldapRealm, $iniRealm --> You can login with a user from LDAP or with a user specified in the [users] section in the configuration file shiro.ini $ldapRealm1,$ldapRealm2 --> You can login with a user coming from the LDAP server specified in the ldap1 realm or coming from the LDAP server coming from LDAP server specified in the ldap2 realm.
|
[main]
...
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.contextFactory.url = ldap://myHost:389
ldapRealm.useStartTls = true
ldapRealm.hostNameVerification = off
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
...
Authentication
With the authentication you will check for a valid username/password combination. To achive this, you have to specify the userDnTemplate.
Username
The username is part of the login patterns
- username@domain
- domain\username
- username
Username may have blanks if they are stored in a LDAP directory. Usernames stored in the configuration file shiro.ini may not have blanks.
When refering to usernames from the LDAP directory to keys in the [users] section to assign roles to the user, you have to change blanks to %20. The password must be empty. When you login with a domain the reference must contain the whole domain/username pattern e.g. user@domain
Configuration in the configuration file shiro.ini
Examples:
- Example
ldapRealm.userDnTemplate = uid={0},ou=People, dc=sos
- Configuration with public LDAP Server
publicLdapRealm.userDnTemplate = uid={0},dc=example,dc=com
- Configuration with a Microsoft AD
adLdapRealm.userDnTemplate = sAMAccountName={0},dc=company,dc=com
ldapRealm.userDnTemplate = {}
Verification with ldapSearch
In all ldapSearch examples the option -x is used. It is possible that your LDAP Server does not allow this and you have to specify a user and a password like:
ldapsearch -h ldap.forumsys.com -p 389 -b "uid=gauss,dc=example,dc=com" -W -D "uid=gauss,dc=example,dc=com"
You can check you userDnTemplate with this ldapSearchCommand.
ldapsearch -h localhost -p 389 -b "uid=ur,ou=People, dc=sos" -x
Should give a result like:
# ur, People, sos
dn: uid=ur,ou=People,dc=sos
mail: uwe.risse@sos-berlin.com
uid: ur
givenName: Uwe
objectClass: top
objectClass: person
objectClass: organizationalPerson
objectClass: inetorgperson
sn: Risse
cn: Uwe Risse
preferredLanguage: de
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1
Example with the public server
ldapsearch -h ldap.forumsys.com -p 389 -b "uid=gauss,dc=example,dc=com" -x
# extended LDIF
#
# LDAPv3
# base <uid=gauss,dc=example,dc=com> with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# gauss, example.com
dn: uid=gauss,dc=example,dc=com
objectClass: inetOrgPerson
objectClass: organizationalPerson
objectClass: person
objectClass: top
cn: Carl Friedrich Gauss
sn: Gauss
uid: gauss
mail: gauss@ldap.forumsys.com
# search result
search: 2
result: 0 Success
# numResponses: 2
# numEntries: 1
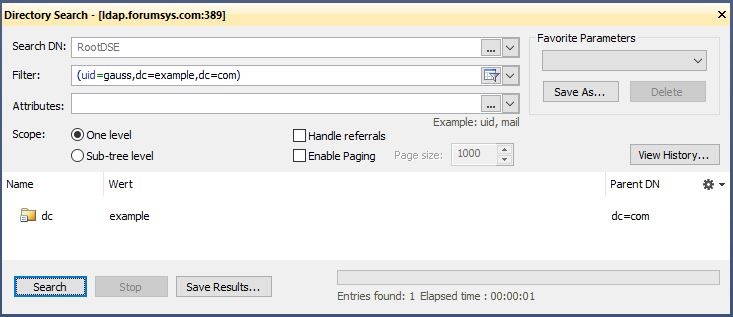
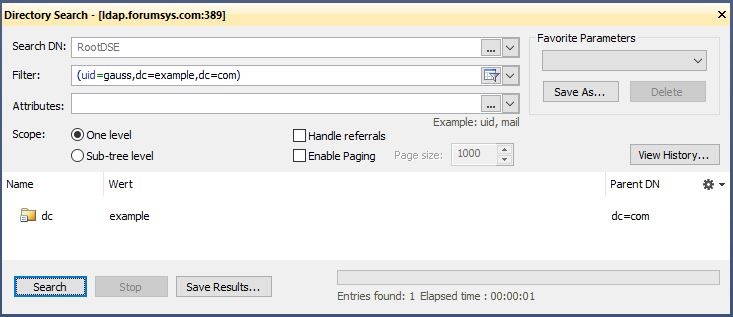
Verification mit Softerra LDAP Browser
Search from root with the userDnTemplate as the user search filter. You should find exactly one entry.
Authorization
Assigning roles from shiro.ini
Assiging roles from LDAP Groups
The group roles mapping
Identifying the group of the user
Using member of with User Search
Using group search
Using more than one LDAP server
LDAP Authentication
Please note that:
- Roles for users that are authenticated via LDAP can be specified in the
[users] section of the shiro.ini without a password.
- The
[users] section can be deleted if roles from the shiro.ini are not to be used at all.
The [main] section contains the following information:
- specification of the LDAP directory service,
- a mapping of the JOC Cockpit role names specified in the
[roles] section of the file onto LDAP group names and - a session timeout.
Getting the roles for a user account
You have to specify:
ldapRealm.userDnTemplate = cn={0},CN=mycn,DC=localhost
ldapRealm.searchBase = CN=mycn,DC=localhost
ldapRealm.contextFactory.url = ldap://localhost:389
#ldapRealm.groupNameAttribute=memberOf
#ldapRealm.userNameAttribute=cn
ldapRealm.groupRolesMap = \
"CN=??????,OU=?????,OU=?????,OU=?????,DC=domain,DC=local":"all"
ldapRealm.userSearchFilter=(&(objectClass=User)(cn=%s))+
%s will be substituted by the user account.
To get the correct values for ldapRealm.userDnTemplate, ldapRealm.searchBase and ldapRealm.userSearchFilter
- please create a query that finds all groups the user account is a member of
- set ldapRealm.userSearchFilter to this query with %s for the user name.
- Example:
(&(objectClass=User)(cn=%s))
- Example:
(uniqueMember=uid=%s,dc=example,dc=com)
- Then identify the attribute in the result that contains the groupName
- set ldapReal.groupNameAttribute to this value (default is memberOf)
- Then assign the value of attribute specified in groupNameAttribute to the groupRolesMap
- Example:
ldapRealm.groupRolesMap="value in attribute groupNameAttribute":"it_operator
- The userDnTemplate is identifiying the user entry in LDAP (e.g. the value of uniqueMember)
Simple Example LDAP Configuration
An example for LDAP configuration is provided with the listing below:
[main]
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = cn={0},cn=myLDAPFolder,dc=localhost
ldapRealm.searchBase = cn=myLDAPFolder,dc=localhost
ldapRealm.contextFactory.url = ldap://localhost:389
#ldapRealm.groupNameAttribute=memberOf
#ldapRealm.userNameAttribute=cn
ldapRealm.userSearchFilter=(&(objectClass=user)(cn=%s))
# Mapping of a LDAP group to roles. You can assign more than one role with separator sign |
ldapRealm.groupRolesMap = \
"cn=JobScheduler_it_operator,cn=Roles,cn=myLDAPFolder,dc=localhost":"it_operator", \
"cn=jobscheduler_admin,cn=Roles,cn=myLDAPFolder,dc=localhost":"administrator|application_manager"
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
# Session timeout in milliseconds
securityManager.sessionManager.globalSessionTimeout = 360000
Example of an Active Directory (AD) LDAP Configuration
[main]
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = cn={0},OU=myOu,OU=Department,DC=myDc1,DC=myDc2,DC=myDc3,DC=myDc4,DC=de
ldapRealm.searchBase = OU=myOu,OU=Department,DC=myDc1,DC=myDc2,DC=myDc3,DC=myDc4,DC=de
ldapRealm.contextFactory.url = ldap://xx.xx.xxx.xx:369
ldapRealm.groupNameAttribute=department
ldapRealm.userSearchFilter=(&(objectClass=*)(cn=%s))
# Mapping of a LDAP group to roles. You can assign more than one role with separator sign |
ldapRealm.groupRolesMap = \
"Information Role":"all"
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
It should only be necessary for system administrators to modify three parts of this section:
- the LDAP directory service information in lines 4 to 6 of the listing,
- the mapping of LDAP groups to roles - here occupying lines 13 to 16 and which is described in the next sub-section and
- the timeout setting for sessions as shown in the last line of the listing and which is specified in milliseconds.
Example Mapping LDAP Groups to Roles:
- In line 15 of the first listing above members of the JobScheduler_it_operator LDAP group are assigned the it_operator role
- More than one role can be specified for members of an LDAP group - for example:
- in line 16 of the first listing members of the LDAP jobscheduler_admin group are assigned the roles of administrator and application_manager.
Example LDAP Configuration with a public LDAP Server
There are many ways of configuring LDAP authentication and authorization. The method you use depends on the structure of groups and users in your LDAP Server. You will find a working example for use with a public LDAP Server described on:
We cannot guarantee that the public LDAP Server will always be online, however, if you struggle with LDAP configuration then you might want to give it a try to have a working example.
To use this example:
- Make a backup of your current shiro.ini file and then copy the contents of the example code block into your shiro.ini file.
- Restart your web services server.
- Log into the JOC Cockpit using the "gauss" account name and the password "password".
[users]
gauss=, all
[main]
# Public LDAP Server for testing purposes
# see http://www.forumsys.com/en/tutorials/integration-how-to/ldap/online-ldap-test-server/
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = uid={0},dc=example,dc=com
ldapRealm.searchBase = dc=example,dc=com
ldapRealm.contextFactory.url = ldap://ldap.forumsys.com:389
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
# Session timeout in milliseconds
securityManager.sessionManager.globalSessionTimeout = 360000
[roles]
# Permissions can be assigned to roles with a comma separated list of permissions. Permissions may have * as a wildcard
all = sos:products
Example LDAP Configuration with a public LDAP Server and mixed LDAP and Shiro Authentication
The following code block is a copy of the short example above showing the authentication of a single LDAP user account, gauss, and an additional Shiro-authenticated administrator user account.
- The Shiro-authenticated user account has been added to the [users] section as normal.
- Note that line 21 of the listing has been modified to read:
[users]
gauss=, all
administrator= secret, administrator
[main]
# Public LDAP Server for testing purposes
# see http://www.forumsys.com/en/tutorials/integration-how-to/ldap/online-ldap-test-server/
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = uid={0},dc=example,dc=com
ldapRealm.searchBase = dc=example,dc=com
ldapRealm.contextFactory.url = ldap://ldap.forumsys.com:389
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm, $iniRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
# Session timeout in milliseconds
securityManager.sessionManager.globalSessionTimeout = 360000
[roles]
# Permissions can be assigned to roles with a comma separated list of permissions. Permissions may have * as a wildcard
all = sos:products
administrator = sos:products:joc_cockpit:jobscheduler_master:view, \
sos:products:joc_cockpit:jobscheduler_master:execute:pause, \
sos:products:joc_cockpit:jobscheduler_master:execute:continue, \
sos:products:joc_cockpit:jobscheduler_master:execute:restart, \
sos:products:joc_cockpit:jobscheduler_master:execute:terminate, \
sos:products:joc_cockpit:jobscheduler_master:execute:abort, \
sos:products:joc_cockpit:jobscheduler_master:administration:edit_permissions, \
sos:products:joc_cockpit:jobscheduler_master:administration:remove_old_instances, \
sos:products:joc_cockpit:jobscheduler_master_cluster, \
sos:products:joc_cockpit:jobscheduler_universal_agent
[main]
# Public LDAP Server for testing purposes
# see http://www.forumsys.com/en/tutorials/integration-how-to/ldap/online-ldap-test-server/
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = uid={0},dc=example,dc=com
ldapRealm.searchBase = dc=example,dc=com
ldapRealm.contextFactory.url = ldap://ldap.forumsys.com:389
ldapRealm.groupNameAttribute=ou
ldapRealm.userNameAttribute=uid
ldapRealm.userSearchFilter=(uniqueMember=uid=%s,dc=example,dc=com)
# Mapping of a LDAP group to roles. You can assign more than one role with separator sign |
ldapRealm.groupRolesMap = \
"scientists":"it_operator", \
"mathematicians":"administrator|application_manager"
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
# Session timeout in milliseconds
securityManager.sessionManager.globalSessionTimeout = 360000
Example LDAP Configuration with Several LDAP Servers
LDAP configuration with several LDAP servers is achieved by defining more than one LDAP realm as shown in the next code block.
ldapRealm1 = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm1.userDnTemplate = cn={0},cn=sos,dc=berlin,dc=com
ldapRealm1.searchBase = cn=sos,dc=berlin,dc=com
ldapRealm1.contextFactory.url = ldap://host1:389
ldapRealm1.groupNameAttribute = ou
ldapRealm1.userNameAttribute = cn
ldapRealm1.userSearchFilter = (cn=%s,cn=sos,dc=berlin,dc=com)
ldapRealm2 = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm2.userDnTemplate = cn={0},cn=sos,dc=berlin,dc=com
ldapRealm2.searchBase = cn=sos,dc=berlin,dc=com
ldapRealm2.contextFactory.url = ldap://host2:389
ldapRealm2.groupNameAttribute = ou
ldapRealm2.userNameAttribute = cn
ldapRealm2.userSearchFilter = (cn=%s,cn=sos,dc=berlin,dc=com)
securityManager.realms = $ldapRealm1, $ldapRealm2
Assigning roles in the shiro.ini when using LDAP
It is possible to mix LDAP authentication with local authorization from a shiro.ini file.
- In the
[users] section- specify the user name but do not specify a password for the user.
- specify the list of roles that are assigned to this user.
- Important: The assignment must start with a comma to skip the password assignment.
- In the
[main] section
Example LDAP Configuration for a public LDAP Server with local roles
[users]
gauss=, application_manager, my_role
newton=, incident_manager, my_role
[main]
# Public LDAP Server for testing purposes
# see http://www.forumsys.com/en/tutorials/integration-how-to/ldap/online-ldap-test-server/
# Active Directory realm configuration
# See http://shiro.apache.org/static/current/apidocs/org/apache/shiro/realm/activedirectory/ActiveDirectoryRealm.html
ldapRealm = com.sos.auth.shiro.SOSLdapAuthorizingRealm
ldapRealm.userDnTemplate = uid={0},dc=example,dc=com
ldapRealm.searchBase = dc=example,dc=com
ldapRealm.contextFactory.url = ldap://ldap.forumsys.com:389
ldapRealm.groupNameAttribute=ou
ldapRealm.userNameAttribute=uid
ldapRealm.userSearchFilter=(uniqueMember=uid=%s,dc=example,dc=com)
# Mapping of a LDAP group to roles. You can assign more than one role with separator sign |
# In this example the LDAP group mapping is commented out. The user gauss will have the roles application_manager and my_role.
# You can mix both role sources, the shiro.ini file and the LDAP group mapping.
# ldapRealm.groupRolesMap = \
# "scientists":"it_operator", \
# "mathematicians":"administrator|application_manager"
rolePermissionResolver = com.sos.auth.shiro.SOSPermissionResolverAdapter
rolePermissionResolver.ini = $iniRealm
ldapRealm.rolePermissionResolver = $rolePermissionResolver
securityManager.realms = $ldapRealm
cacheManager = org.apache.shiro.cache.MemoryConstrainedCacheManager
securityManager.cacheManager = $cacheManager
# Session timeout in milliseconds
securityManager.sessionManager.globalSessionTimeout = 360000
[roles]
# Permissions can be assigned to roles with a comma separated list of permissions. Permissions may have * as a wildcard
all = sos:products
administrator = sos:products:joc_cockpit:jobscheduler_master:view, \
sos:products:joc_cockpit:jobscheduler_master:execute:pause, \
sos:products:joc_cockpit:jobscheduler_master:execute:continue, \
sos:products:joc_cockpit:jobscheduler_master:execute:restart, \
sos:products:joc_cockpit:jobscheduler_master:execute:terminate, \
sos:products:joc_cockpit:jobscheduler_master:execute:abort, \
sos:products:joc_cockpit:jobscheduler_master:administration:edit_permissions, \
sos:products:joc_cockpit:jobscheduler_master:administration:remove_old_instances, \
sos:products:joc_cockpit:jobscheduler_master_cluster, \
sos:products:joc_cockpit:jobscheduler_universal_agent
application_manager = sos:products:joc_cockpit:jobscheduler_master:view, \
sos:products:joc_cockpit:jobscheduler_master:execute:pause, \
sos:products:joc_cockpit:jobscheduler_master:execute:continue, \
sos:products:joc_cockpit:jobscheduler_master:administration:manage_categories, \
sos:products:joc_cockpit:jobscheduler_master_cluster:view:status, \
sos:products:joc_cockpit:jobscheduler_universal_agent:view:status, \
sos:products:joc_cockpit:daily_plan:view:status, \
sos:products:joc_cockpit:history:view, \
sos:products:joc_cockpit:order, \
sos:products:joc_cockpit:job_chain, \
sos:products:joc_cockpit:job, \
sos:products:joc_cockpit:process_class, \
sos:products:joc_cockpit:schedule, \
sos:products:joc_cockpit:lock, \
sos:products:joc_cockpit:event, \
sos:products:joc_cockpit:event_action, \
sos:products:joc_cockpit:holiday_calendar:view:status, \
sos:products:joc_cockpit:maintenance_window:view, \
sos:products:joc_cockpit:maintenance_window:enable_disable_maintenance_window, \
sos:products:joc_cockpit:audit_log:view:status, \
sos:products:joc_cockpit:customization:share
it_operator = sos:products:joc_cockpit:jobscheduler_master:view, \
sos:products:joc_cockpit:jobscheduler_master_cluster:view:status, \
sos:products:joc_cockpit:jobscheduler_universal_agent:view:status, \
sos:products:joc_cockpit:daily_plan:view:status, \
sos:products:joc_cockpit:history:view, \
sos:products:joc_cockpit:order, \
sos:products:joc_cockpit:job_chain, \
sos:products:joc_cockpit:job, \
sos:products:joc_cockpit:process_class, \
sos:products:joc_cockpit:schedule, \
sos:products:joc_cockpit:lock, \
sos:products:joc_cockpit:event, \
sos:products:joc_cockpit:event_action, \
sos:products:joc_cockpit:holiday_calendar:view:status, \
sos:products:joc_cockpit:maintenance_window:view, \
sos:products:joc_cockpit:audit_log:view:status, \
sos:products:joc_cockpit:customization:share:view
incident_manager = sos:products:joc_cockpit:jobscheduler_master:view, \
sos:products:joc_cockpit:jobscheduler_master_cluster:view:status, \
sos:products:joc_cockpit:jobscheduler_universal_agent:view:status, \
sos:products:joc_cockpit:daily_plan:view:status, \
sos:products:joc_cockpit:history:view, \
sos:products:joc_cockpit:order:view, \
sos:products:joc_cockpit:order:remove_setback, \
sos:products:joc_cockpit:job_chain:view, \
sos:products:joc_cockpit:job:view, \
sos:products:joc_cockpit:process_class:view, \
sos:products:joc_cockpit:schedule:view, \
sos:products:joc_cockpit:lock:view, \
sos:products:joc_cockpit:event:view, \
sos:products:joc_cockpit:event_action:view, \
sos:products:joc_cockpit:holiday_calendar:view:status, \
sos:products:joc_cockpit:maintenance_window:view, \
sos:products:joc_cockpit:audit_log:view:status, \
sos:products:joc_cockpit:customization:share:view
business_user = sos:products:joc_cockpit:jobscheduler_master:view:status, \
sos:products:joc_cockpit:jobscheduler_master_cluster:view:status, \
sos:products:joc_cockpit:jobscheduler_universal_agent:view:status, \
sos:products:joc_cockpit:daily_plan:view:status, \
sos:products:joc_cockpit:history:view, \
sos:products:joc_cockpit:order:view:status, \
sos:products:joc_cockpit:order:view:order_log, \
sos:products:joc_cockpit:job_chain:view:status, \
sos:products:joc_cockpit:job_chain:view:history, \
sos:products:joc_cockpit:job:view:status, \
sos:products:joc_cockpit:job:view:history, \
sos:products:joc_cockpit:job:view:task_log, \
sos:products:joc_cockpit:process_class:view:status, \
sos:products:joc_cockpit:schedule:view:status, \
sos:products:joc_cockpit:lock:view:status, \
sos:products:joc_cockpit:holiday_calendar:view:status, \
sos:products:joc_cockpit:maintenance_window:view:status, \
sos:products:joc_cockpit:audit_log:view:status, \
sos:products:joc_cockpit:customization:share:view
api_user = sos:products:commands:jobscheduler_master:view:status, \
sos:products:commands:history:view, \
sos:products:commands:order, \
sos:products:commands:job_chain, \
sos:products:commands:job, \
-sos:products:commands:job:view:configuration, \
-sos:products:commands:job_chain:view:configuration, \
-sos:products:commands:order:view:configuration, \
-sos:products:commands:order:remove_setback, \
sos:products:commands:process_class:view:status, \
sos:products:commands:schedule:view:status, \
sos:products:commands:lock:view:status, \
sos:products:commands:holiday_calendar:view:status, \
sos:products:commands:maintenance_window:view:status
my_role = sos:products:commands:jobscheduler_master:view:status, \
sos:products:joc_cockpit:history:view, \
sos:products:joc_cockpit:order:view:status