Page History
| Table of Contents |
|---|
Configuring the
...
JOC Cockpit
Consider Note that it is not required necessary to configure a Controller the JOC Cockpit - it runs out-of-the-box. Zero The default configuration includes that:
- specifies HTTP connections which are used to
- deployment of objects, e.g. workflows and jobs, is not subject to compliance requirements such as non-repudiation.
- HTTP connections are used that expose unencrypted communication between clients and the JOC Cockpit and Controller. Authentication is performed by hashed passwords.
Users who intend to operate a compliant and secure job scheduling environment should consider the information provided below explanations for
- deployment of objects with digital signatures that can be used to restrict and to verify who deploys a given object such as a workflow.
- HTTPS connections that encrypt communication and that include mutual authentication by certificates without use of passwords.
Compliance: Use of Signing Certificates
Controller instances accept deployments for a number of objects such as workflows from a JOC Cockpit instance only if such objects are digitally signed.
- If JOC Cockpit is operated for Security Level Low then a single X.509 private key assigned to the JOC Cockpit
rootaccount is used to sign any objects by any JOC Cockpit accounts. - If JOC Cockpit is operated for Security Level Medium or High then each account that deploys objects has to own an individual X.509 private key or PGP private key.
To verify the signature of an object the Controller has to apply the public key or certificate that matches the private key used for signing with JOC Cockpit.
- If X.509 private keys are used for signing of objects then the Root CA Certificate or Intermediate CA Certificate that was used to sign the respective private key has to be in place with the Controller.
- If PGP private keys are used for signing of objects then the public key matching the signing key has to be in place with the Controller.
- The Controller expects certificates/public keys from the following locations:
- X.509 Certificates
- Location
- Windows:
C:\ProgramData\sos-berlin.com\js7\controller\var\config\private\trusted-x509-keys - Unix:
/var/sos-berlin.com/js7/controller/var/config/private/trusted-x509-keys
- Windows:
- The expected X.509 certificate format is PEM. Certificates can be added from any file names with the extension
.pem. - Consider that instead of individual certificates per signing key the Root CA Certificate or Intermediate CA Certificate that was used to sign the private keys is sufficient.
- Location
- PGP Public Keys
- Location
- Windows:
C:\ProgramData\sos-berlin.com\js7\controller\var\config\private\trusted-pgp-keys - Unix:
/var/sos-berlin.com/js7/controller/var/config/private/trusted-pgp-keys
- Windows:
- PGP public keys are expected in ASCII armored format. They can be added from any file names with the extension
.asc. - Consider that for each PGP private key that is used for signing the corresponding public key has to be available with the Controller instance.
- Location
- By default the Controller ships with an X.509 certificate of SOS that matches the default signing key available with the JOC Cockpit
rootaccount.
- X.509 Certificates
- In order to add individual certificates/public keys add the respective files to the above location corresponding the key type. To revoke certificates/public keys accordingly remove the respective files from the above location matching the key type.
- The above locations for certificates/public keys can be accessed from the Docker volume specified with the
--mountoption for the Controller's container directory/var/sos-berlin.com/js7/controller/var/config. The locations for X.509 certificates and PGP public keys are available from sub-directories.
Security: Use with HTTPS Connections
The Controller by default is prepared for connections by JOC Cockpit instances using the HTTP and the HTTPS protocols.
...
covering:
- HTTPS connections that encrypt communication between clients, e.g. user browsers, and the JOC Cockpit. In addition, refer to the JOC Cockpit - Two-factor Authentication article.
- HTTPS connections between JOC Cockpit and Controller instances for mutual authentication.
Security: Use with HTTPS Connections
By default, the JOC Cockpit is configured for connections using the HTTP and the HTTPS protocols. HTTPS connections are used in two ways:
- The JOC Cockpit is accessed by clients using the HTTPS protocol.
- The JOC Cockpit connects to the Controller using the HTTPS protocol with mutual authentication.
Note that the following prerequisites have to be fulfilled before order activating HTTPS:
| Info | ||
|---|---|---|
| ||
If you are new to certificate management or are looking for a solution that works out-of-the-box then you can use the configuration from the attached archives:
|
Provide Keystore, Truststore and Configuration
...
Connections to Controller JOC Cockpit instances are established from a JOC Cockpit instancea client, e.g. a user browser. If the HTTPS protocol is used then in addition to securing the communication channel the Controller instance requires mutual authentication.
Controller Keystore and Truststore
note that clients have to hold the server certificate in their truststore. For CA signed server certificates, clients can use the root CA certificate or intermediate CA certificate that signed the server certificate.
- The JOC Cockpit The Controller instance's private key has to be created for Server Authentication and key usage. If the Controller instance is configured for mutual authentication then the Client Authentication extended key usageskey usage has to be available from the JOC Cockpit instance's private key.
- The Controller instance JOC Cockpit instance is provided with:
- a keystore that holds its private key, certificate, Root CA Certificate and optionally Intermediate CA Certificate.
- a truststore that holds the certificate chain - consisting of Root CA Certificate and optionally Intermediate CA Certificate - required to verify the Controller's certificate.
- Keystores and truststores are files in PKCS12 format, usually with a .p12 extension. They should be added to the following locations:
- Keystore:
- Windows:
C:\ProgramData\sos-berlin.com\js7\controllerjoc\varresources\configjoc\private\https-keystore.p12 - Unix:
/var/sos-berlin.com/js7/controllerjoc/varresources/config/privatejoc/https-keystore.p12
- Windows:
- Truststore:
- Windows:
C:\ProgramData\sos-berlin.com\js7\controllerjoc\varresources\configjoc\private\https-truststore.p12 - Unix:
/var/sos-berlin.com/js7/controllerjoc/varresources/config/privatejoc/https-truststore.p12
- Windows:
- Keystore:
Controller Configuration
The default configuration of JOC Cockpit ships with the above keystore and truststore files. Users can add their private keys and certificates to the relevant keystore/truststore. The corresponding configuration items are in place by default.
JOC Cockpit Keystore and Truststore for Client Connections
The JOC Cockpit instance's
The Controller instance'sstart.iniconfiguration file by default holdsprivate.confconfiguration file has to be addedthe following configuration items. For details
seesee the JS7 -
ControllerJOC Cockpit Configuration Items
Mutual Authenticationarticle.
ControllerCode Block language bash title
Mutual AuthenticationJOC Cockpit Configuration for
js7Keystore and Truststore Locations with HTTPS Client Connections linenumbers true
{##
Keystore file path (relative to $jetty.base) jetty.sslContext.keyStorePath=resources/joc/https-keystore.p12 ## Truststore file path (relative to $jetty.base) jetty.sslContext.trustStorePath=resources/joc/https-truststore.p12 ## Keystore password jetty.sslContext.keyStorePassword=jobscheduler ## KeyManager password (same as keystore password for pkcs12 keystore type) jetty.sslContext.keyManagerPassword=jobscheduler ## Truststore password jetty.sslContext.trustStorePassword=jobscheduler ## Connector port to listen on jetty.ssl.port=4443
- Keystore and truststore locations:
- The configuration items listed above specify the locations of the keystore and the truststore.
- Consider the optional use of a key password and store password for keystores and the use of a store password for truststores.
JOC Cockpit Keystore and Truststore for Controller Connections
The JOC Cockpit instance's
auth { # User accounts for https connections users { # Controller account for connections by primary/secondary JOC Cockpit instance Controller { distinguished-names=[ "DNQ=SOS CA, CN=js7-joc-primary, OU=IT, O=SOS, L=Berlin, ST=Berlin, C=DE", "DNQ=SOS CA, CN=js7-joc-secondary, OU=IT, O=SOS, L=Berlin, ST=Berlin, C=DE" ] } } }joc.propertiesconfiguration file by default holds the following configuration items. For details see the JS7 - JOC Cockpit Configuration Items article.- This setting specifies the distinguished names that are available from the subjects of JOC Cockpit certificates. Consider that the common name (CN) attribute specifies the hostname of a JOC Cockpit instance. The configuration authenticates a given JOC Cockpit instance as the distinguished name is unique for a server certificate and therefore replaces use of passwords. Keystore and truststore locations:
- The above configuration items specify the locations of keystore and truststore.
- Consider optional use of a key password and store password for keystores and of a store password for truststores.
| Code Block | |||
|---|---|---|---|
|
|
|
################################################################################ ### Location, type and |
password |
of the Java truststore which contains the ### certificates |
of |
each |
JS7 |
Controller |
for HTTPS connections |
. Path can be ### absolute or relative to |
this |
file. keystore_path = ../../resources/joc/https-keystore.p12 |
keystore_type = PKCS12 keystore_password |
= jobscheduler key_password = jobscheduler truststore_path = ../../resources/joc/https-truststore.p12 |
...
truststore_type = PKCS12 truststore_password = jobscheduler- This setting specifies the location of the keystore and truststore.
Run JOC Cockpit Container for HTTPS Connections
The following additional arguments are required for HTTPS connections:
| Code Block | ||||||
|---|---|---|---|---|---|---|
| ||||||
#!/bin/sh
docker run -dit --rm \
...
--publish=1544317443:4443 \
--env="RUN_JS_HTTPS_PORT=4443" \
... |
ExplanationsExplanation:
--publishThe Controller JOC Cockpit image is prepared configured to accept HTTPS requests on port4443. If the Controller JOC Cockpit instance is not operated in a Docker container network then an outside port of the Docker container's host has to be mapped to the inside HTTPS port4443. The same port has to be assigned theRUN_JS_HTTPS_PORTenvironment variable.--env=RUN_JS_HTTPS_PORTThe port assigned this environment variable is the same as the inside HTTPS port specified with the--publishoption.
...
- When using HTTPS connections then , consider to drop dropping the HTTP port of the Controller instance JOC Cockpit instance by omitting the following from the settings listed above settings:
--publish=1544417446:4444This4446This mapping should be dropped in order to prevent incoming traffic to the Controller JOC Cockpit instance's HTTP port.
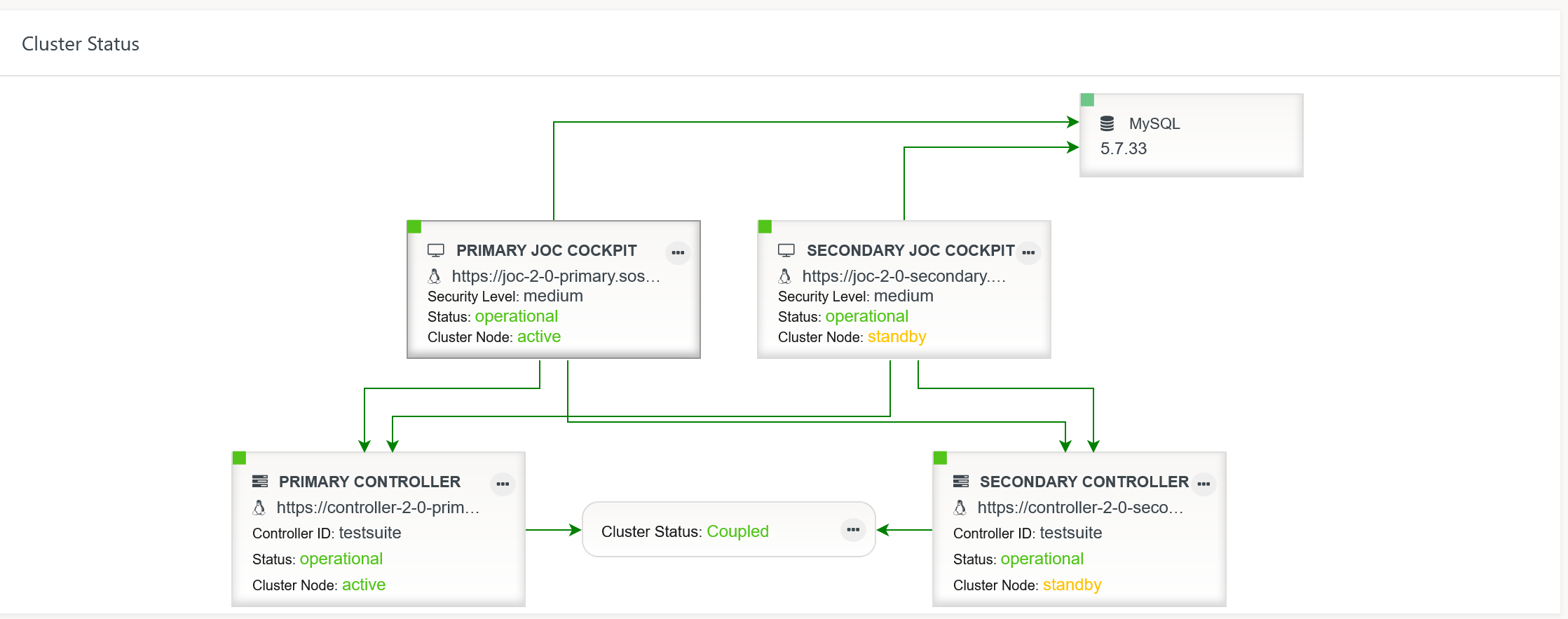
High Availability: Operating a Cluster
JOC Cockpit can be operated as a passive cluster for high availability.
- Note that the clustering operational feature is subject to the JS7 - License. Without a license:
- fail-over/switch-over will not take place between JOC Cockpit cluster members.
- you have to (re)start a Secondary JOC Cockpit instance if you want this instance to become active after the Primary JOC Cockpit instance has shutdown or become unavailable.
- The installation of JOC Cockpit cluster members is the same as explained with the JS7 - JOC Cockpit Installation for Containers article.
- Both Primary and Secondary JOC Cockpit containers can be started from the same image.
- Both JOC Cockpit instances will become visible with each instance's Dashboard View.
To better visually distinguish Primary and Secondary JOC Cockpit instances you can modify the instance title ("Primary JOC Cockpit", "Secondary JOC Cockpit")
- Navigate to the
configvolume that is mounted from the JOC Cockpit container as indicated with the JS7 - JOC Cockpit Installation for Containers article. The volume is mounted to the
/var/sos-berlin.com/js7/joc/resources/jocdirectory and includes the filejoc.properties:Code Block language bash title JOC Cockpit Dashboard configuration with joc.properties linenumbers true ################################################################################ ### If JOC Cockpit is used in a cluster then type a title to identify which node ### is currently used. Further type an ordering (Primary <= 0, Standby > 0) for ### the display order in JOC's dashboard title = PRIMARY JOC COCKPIT ordering = 0- Modify the title of the JOC Cockpit instance as you require.
- Adjust the ordering, i.e. the sequence of JOC Cockpit instances displayed in the Dashboard View from left to right starting with 0.