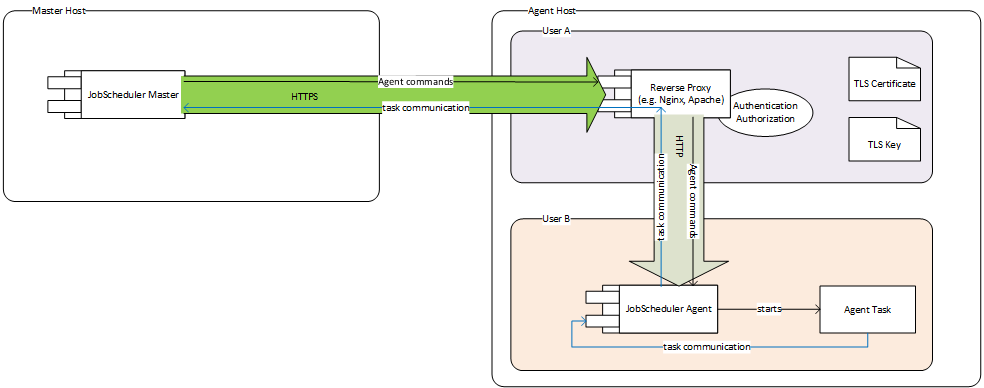
Architecture
Communication to and from the Universal Agent can be secured by HTTPS using a 3rd party reverse proxy (e.g. Apache HTTP Server, nginx).
Explanations
This setup needs 2 user accounts on the agent host:
...
- JobScheduler Master requests a job start on the Agent
- the request goes through https to the reverse proxy
- the reverse proxy forwards the request by http to JobScheduler Agent the same machine
- JobScheduler Agent starts an agent task
- The agent tasks communicates with JobScheduler Master (logging, api calls...)
- the agent task connects by TCP to the JobScheduler Agent
- JobScheduler Agent tunnels all communication from the agent task to JobScheduler Master through the existing HTTP connection to the reverse proxy continuing in the HTTPS connection to JobScheduler Master
Motivation for using a 3rd party reverse proxy
- Separation of confidential credentials from JobScheduler Agent
- Whoever is able to run jobs JobScheduler Agent is able to
- access all files that can be accessed by the user running JobScheduler Agent
- execute all processes that can be executed by the user running JobScheduler Agent
- do whatever the user running JobScheduler Agent could do on the shell
- If the user running JobScheduler Agent was the same user that runs the reverse proxy (or if the proxy was integrated into JobScheduler Agent), he could
- steal the TLS key
- reconfigure the reverse proxy to accept connections from other hosts
- Whoever is able to run jobs JobScheduler Agent is able to
- The JobScheduler Universal Agent aims at a zero-configuration approach
- Setting up TLS encryption needs a lot of configuration (certificates, keys, protocol options)
- Experienced adminstrators know how to configure this in the reverse proxy of their choice (but would have to learn how to do this if it were configured in JobScheduler Agent)
- Use existing trusted functionality
- TLS configuration and handling
- Authentication: simple authentication can be achieved by restricting reverse proxy access to certain hosts
- Authorisation: reverse proxy servers can be configured to allow
- GET and POST requests for some hosts → execution of jobs possible
- only GET request for other hosts → read-only access (status information...)
Security
This setup secures the Agent against:
...
- attackers spoofing the IP of the JobScheduler Master
Possible Enhancements
Validating the client identitiy using HTTPS client authentication
- JobScheduler Master is configured with a client HTTPs certificate
- The reverse proxy is configured to only accept connections from certain hosts which can authenticate with a valid client certificate
...